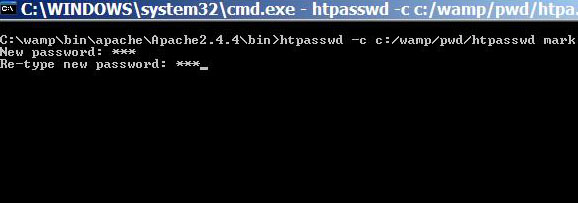
Htaccess file is used to control access to directories in the web server. Normally, website administrators write htaccess file to put appropriate access control to files and pages stored in a specific directory. This method of directory access control is useful when you have a small number of users whom you want to give permission to view your contents. … [Read more...] about How to Control Directory Access with Htaccess and Htpasswd in Apache
Internet Security and Safety
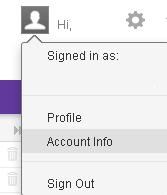
Yahoo Mail Security Settings:How to Protect Your Account
To secure your Yahoo mail account you need to block the doors that are easy for anyone to get access to your account. This post will help you to modify your account settings to make your mailbox safer than ever. If you are a Yahoo mail user, then you are advised to use the following settings: Create a sign-in seal How to change password Monitor your account … [Read more...] about Yahoo Mail Security Settings:How to Protect Your Account
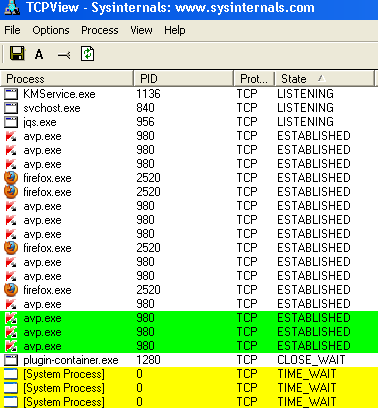
How Do I Know If My Computer Has Been Hacked?
If you know some simple and easy-to-use methods to check that if your computer has been hacked you can confidently work online or visit any site without much worrying about your data privacy. The good news is that there are some simple ways to check that if your system has been hacked, which works well in most of the cases.At first you need to know the ways that can be used to … [Read more...] about How Do I Know If My Computer Has Been Hacked?
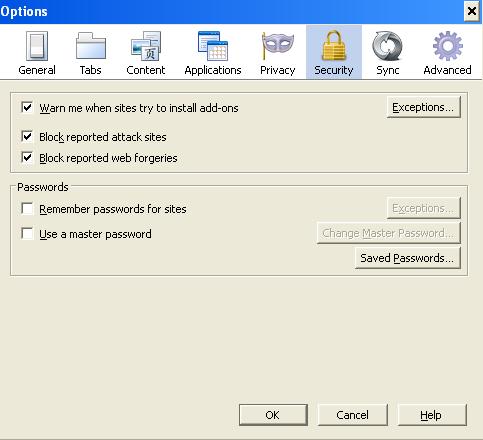
Firefox Security Settings and Features
There are certain security issues that would help you keep your browsing experience smooth and safe with Firefox.As you know that web browser work as a middle man between you and the webpages. When you request for a webpage from your computer by typing a web address (URL), all the underline works such as grabbing the pages and displaying it to you in human readable format is … [Read more...] about Firefox Security Settings and Features
Laptop Security Devices and Tips
Providing physical security to your laptop is your primary concern if you are a frequent travel or on the move. There are a number of devices and precautions that you can take to secure your laptop and even can get back your laptop if it gets stolen. The following are a list of devices and suggestions the you may consider as a solution to your laptop security. … [Read more...] about Laptop Security Devices and Tips
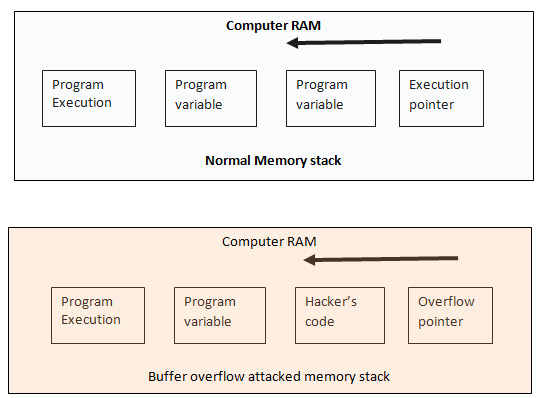
Buffer Overflow Protection Tutorial
When you write a simple program, for example, to print user name with greetings. For this program to run you assign character string 38 in the following way Char name (38) Here “name” is the variable name. The above code specifies that you name or users’ input would not be more than 38 characters long because you have already assigned only 38 bit of data into the buffer. … [Read more...] about Buffer Overflow Protection Tutorial
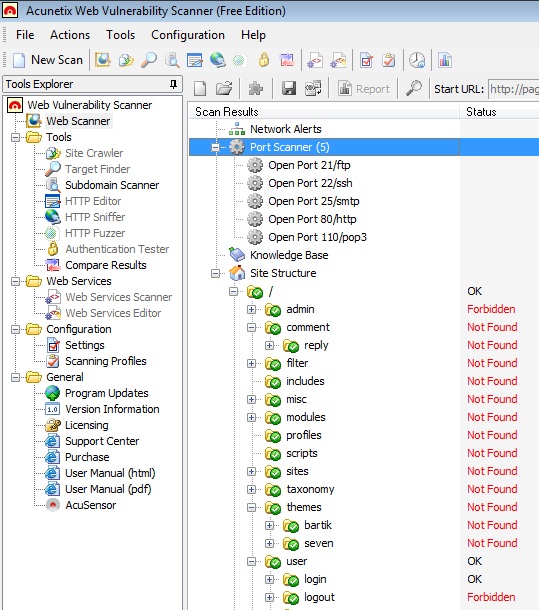
Acunetix Web Vulnerability Scanner to Detect your Website’s Security Loopholes
Acunetix web vulnerability scanner help to find vulnerability in a website so as you can make your site or blog as secure as possible. Acunetix has a free version that you can use to find some of the common vulnerabilities of a website.In this article I will show you how you can use the free version of acunetix to figure out how much secure you blog is.Although Acunetix has a … [Read more...] about Acunetix Web Vulnerability Scanner to Detect your Website’s Security Loopholes
Domain Name Registration Law:You cannot Choose any Trademark name
Literally you can buy any domain name that is available for registration. But that does not mean that you can legally have that domain because if there is any trademark registered for that domain name then you have to give it to that company’s owner when they claim for that domain name. Though most of the new companies try to buy a domain name first before choosing their … [Read more...] about Domain Name Registration Law:You cannot Choose any Trademark name
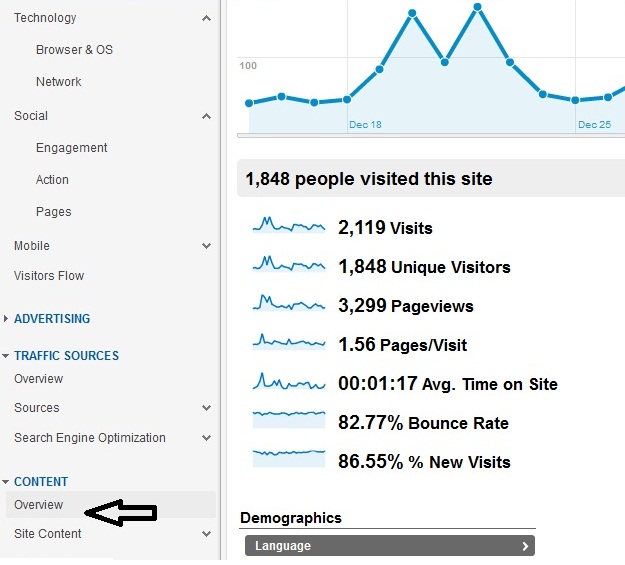
Google Analytics for IT Security Professionals
What is Google Analytics? In short Google analytics is a website statistics tracking tool that you can use to track how your users are interacting with your WebPages such as which pages are being visited the most and where the visitors came from or what keywords he used to find your pages. Who should use Google Analytics? IT professionals( both in operation and security) … [Read more...] about Google Analytics for IT Security Professionals
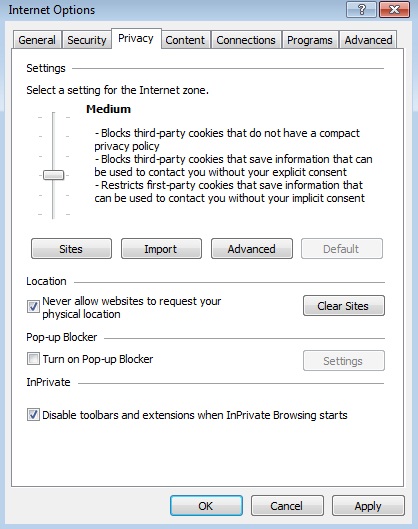
What are Cookies in Web Browser
What are cookies Cookies are a small piece of software or codes that is used by websites to track its users. When you go to a website for the first time then it send a small file to its user’s computer, which tracks the user’s behavior while they visit a website. … [Read more...] about What are Cookies in Web Browser
WordPress Security Best Practices
With every update, WordPress improves its security capabilities and fix the vulnerabilities. As you know that the default configuration is always risky. To secure a site you always need to customize your security settings, which means apply the best security practices for your blogging platform. If you are a new WordPress user, you might go through a steep learning curve … [Read more...] about WordPress Security Best Practices