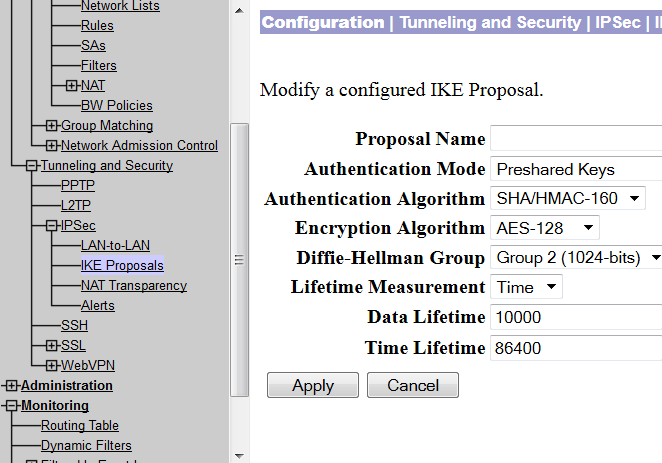
At times, it is economical to build a VPN tunnel with the available networking resources. For example, if you have a VPN concentrator and you need to connect a small office securely with your network, you can do so by installing a low priced Cisco router in the remote office. This post will demonstrate how you can build VPN using a VPN concentrator and a Cisco router. … [Read more...] about Site to Site VPN Between Cisco VPN Concentrator and Router
vpn
What is VPN and How it Works?
By reading this post you can learn about VPN and its workings. VPN is just a term we use to describe a system which makes communication between two computers, regardless of how far they are, within a secure channel. Here the secure channel means you can convert the public network secure. As you know that a public network is nothing but the Internet, where can have access to any … [Read more...] about What is VPN and How it Works?
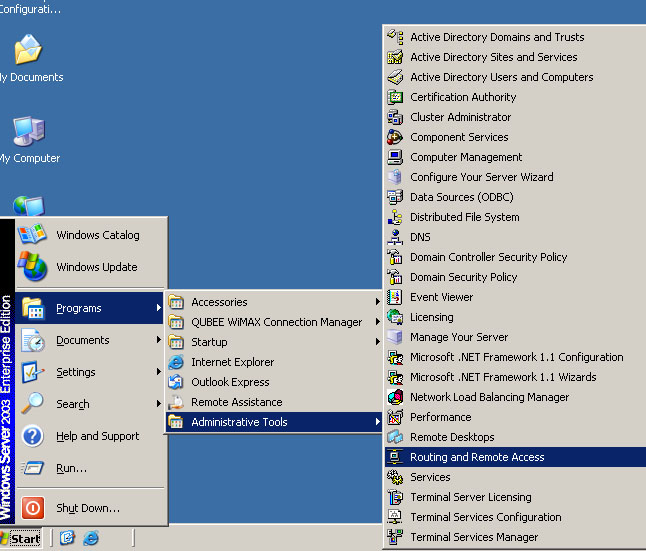
How to Configure VPN,RAS and IPSec Policy in Windows Server
VPN is a trusted and secure network, which use tunneling and protocol(PPTP,L2TPIPSec) to make data transmission through the public network. RAS: remote access service used to access server remotely from client terminal using dial-up connection. IAS:Internet authentication service is used to remotely and centrally manage all RAS server and keep remote access policy … [Read more...] about How to Configure VPN,RAS and IPSec Policy in Windows Server
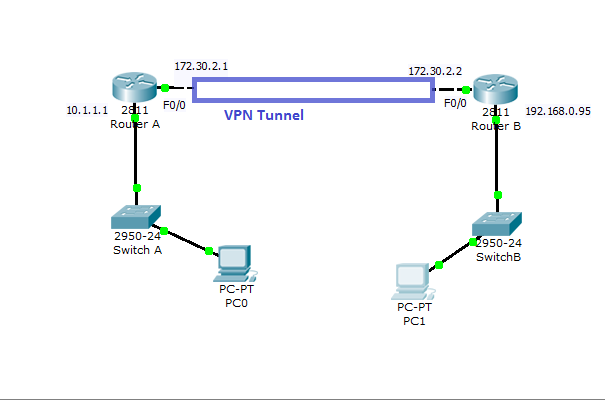
Cisco VPN Configuration in IOS Routers
How to Configure VPN in Cisco Routers Virtual private network can be configured with most of the Cisco routers( 800 to 7500 series) with IOS version 12 or higher.VPN can be implemented in a number of ways--with various level of security measures and configuration. To determine the right VPN configuration for your network, you need to have a solid understanding in cryptographic … [Read more...] about Cisco VPN Configuration in IOS Routers