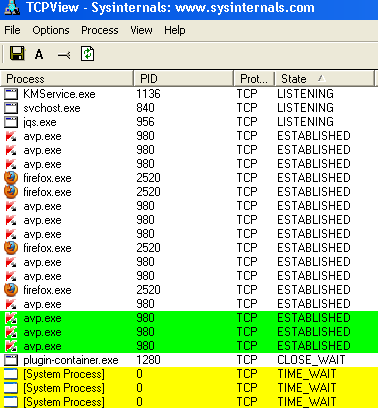
If you know some simple and easy-to-use methods to check that if your computer has been hacked you can confidently work online or visit any site without much worrying about your data privacy. The good news is that there are some simple ways to check that if your system has been hacked, which works well in most of the cases.At first you need to know the ways that can be used to … [Read more...] about How Do I Know If My Computer Has Been Hacked?
computer
Buffer Overflow Protection Tutorial
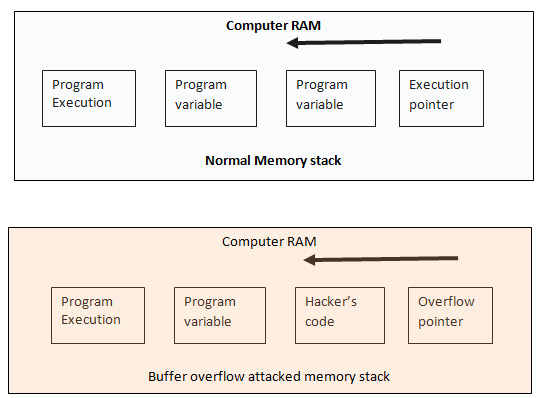
When you write a simple program, for example, to print user name with greetings. For this program to run you assign character string 38 in the following way Char name (38) Here “name” is the variable name. The above code specifies that you name or users’ input would not be more than 38 characters long because you have already assigned only 38 bit of data into the buffer. … [Read more...] about Buffer Overflow Protection Tutorial
Computer Security Essentials
The major threats a computer user may expect are – the damage of his stored data or software and stealing of confidential information. A computer can get infected with malicious programs like virus, Trojan, crimeware, spyware, malware or anything else, but the main challenge in front of you is to keep your all the data safe and also to keep your confidential information private … [Read more...] about Computer Security Essentials