Concept of private VLAN A VLAN allows unrestricted traffic flow among the hosts within the VLAN. When a packet is sent from a host to a destination machine within a VLAN, the switch sends that packet only to the destination host machine, not to every other host in the VLAN. But when a broadcast traffic is sent by a host machine, all other hosts in the VLAN receive the … [Read more...] about How to Configure Cisco Private VLANs in 4 Easy Steps
cisco
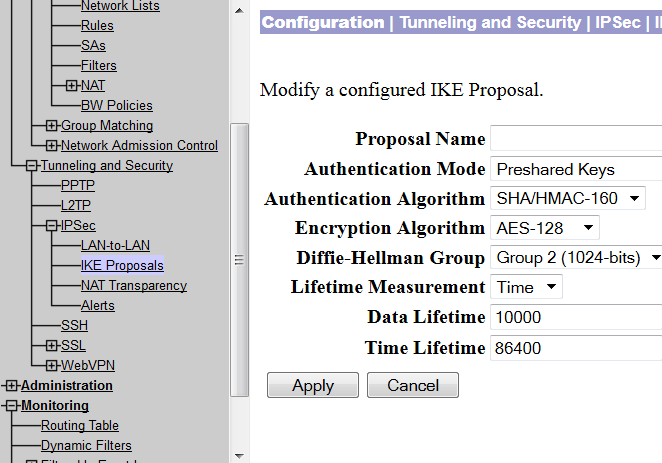
Site to Site VPN Between Cisco VPN Concentrator and Router
At times, it is economical to build a VPN tunnel with the available networking resources. For example, if you have a VPN concentrator and you need to connect a small office securely with your network, you can do so by installing a low priced Cisco router in the remote office. This post will demonstrate how you can build VPN using a VPN concentrator and a Cisco router. … [Read more...] about Site to Site VPN Between Cisco VPN Concentrator and Router
Cisco Router Security Check for Auditor
Since router is the key to access an organization's network from the outside world, the maximum security priority should be given to routers that are connected to the Internet and to the important application servers. ISO-27001 has already defined standard router security checklist, which any organization can use to improve their router securities. This post aims to … [Read more...] about Cisco Router Security Check for Auditor
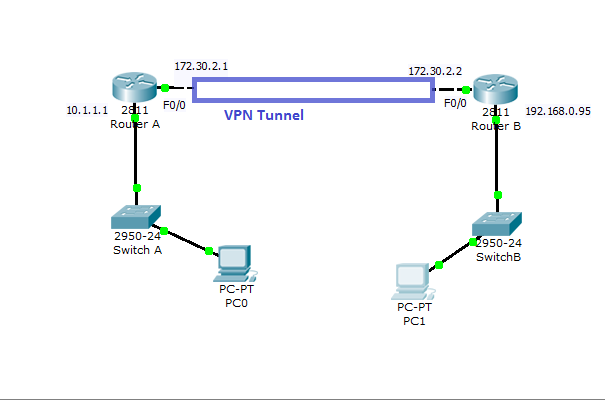
Cisco VPN Configuration in IOS Routers
How to Configure VPN in Cisco Routers Virtual private network can be configured with most of the Cisco routers( 800 to 7500 series) with IOS version 12 or higher.VPN can be implemented in a number of ways--with various level of security measures and configuration. To determine the right VPN configuration for your network, you need to have a solid understanding in cryptographic … [Read more...] about Cisco VPN Configuration in IOS Routers
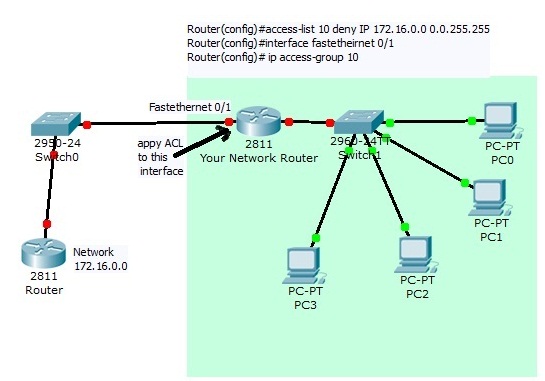
Access Control List Configuration on Cisco Router
What is ACL: Access control list or ACLs are a set of if-then rules set on a router to allow or deny a specific group of IP to send or receive traffic from your network into another network. When you apply an ACL to a route interface for incoming traffic then every incoming packets will be compared with your ACL first, if a match is found then either permit or deny action … [Read more...] about Access Control List Configuration on Cisco Router