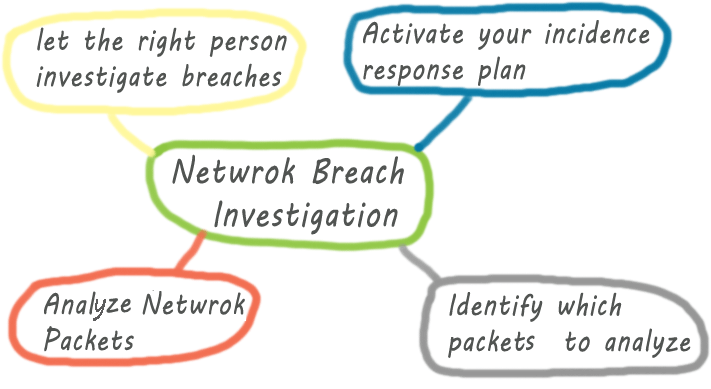
Investigating network security breach may seem to be a daunting task to someone who has no prior experience of security breach investigation. Like any other IT disciplines, you can handle and investigate network security breach better if you have are well-equipped with the necessary tools and techniques used by the professionals. No matter if you are a network engineer or a … [Read more...] about Tips for Network Security Breach Investigation
network
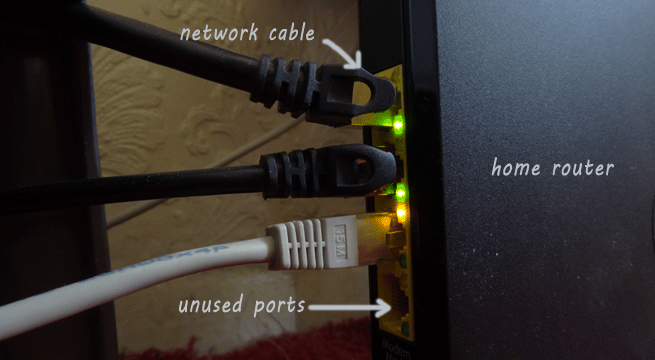
20 Ways to Secure Home Network
Almost every Internet user has their home network that every family member use to Internet access.For your home network security you can follow a few simple steps to eliminate the chances of your network being compromised. Before diving deep into the home network security issues, you may have a look at the vulnerability points in your network, including your client machine. … [Read more...] about 20 Ways to Secure Home Network
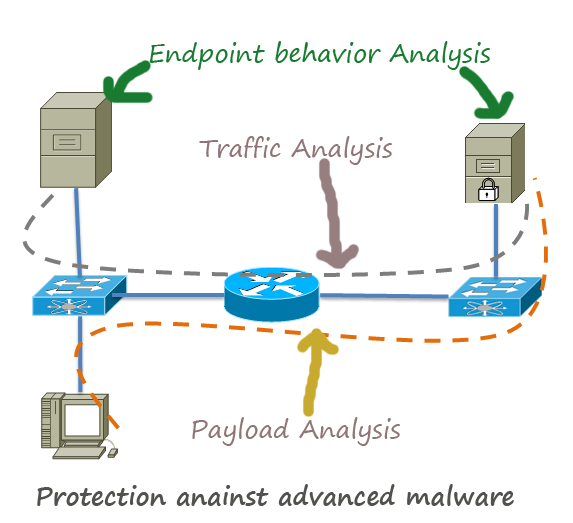
How to Protect Network Against Advanced Malware
Advanced malwares are extremely stealthy and attack targeted protocols and applications. In most cases, the attackers use these malwares to steal sensitive information from the governmental institutes financial institutes, especially the credit card service providers . Major Concerns about Advanced Malware: They are discovered after the attack has been taken place. So, … [Read more...] about How to Protect Network Against Advanced Malware
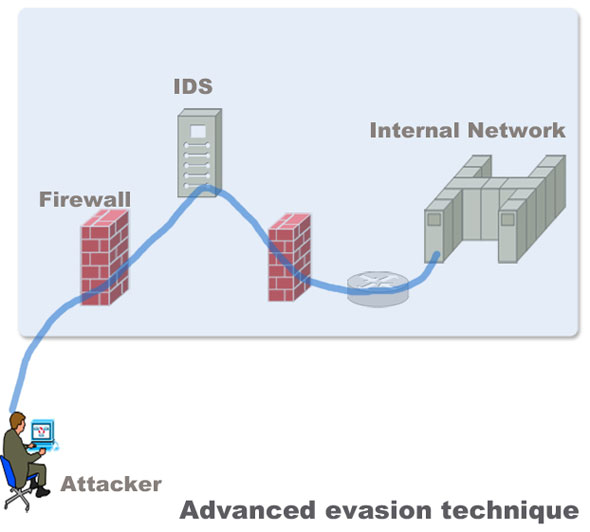
How to Protect Networks against Advanced Evasion Techniques(AET)
Evasion techniques evade the exiting network security devices such as signature based IPS and firewalls to enter the internal network to deliver exploits in servers. Most of the Intrusion detection and prevention system rely on attack signatures to identify malicious strings in the traffic. The strings used to evade the devices are not malicious themselves. Their main purpose … [Read more...] about How to Protect Networks against Advanced Evasion Techniques(AET)
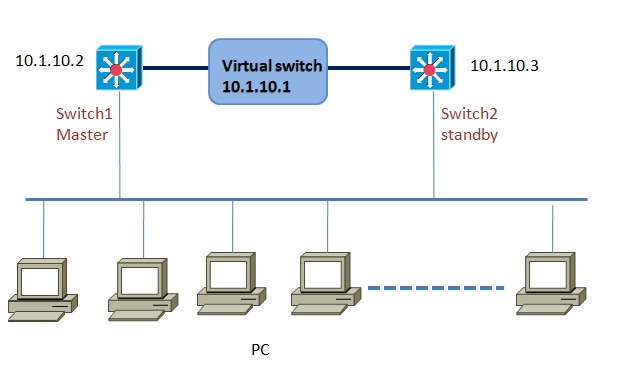
VRRP Configuration(virtual router redundancy protocol)
VRRP or virtual router redundancy protocol provides router or switch interfaces failover and failback facility for seamless operation of a network. VRRP almost similar to HSRP in terms of operations and functions, but with a few added features such as VRRP supports up to 255 groups. Just like HSRP, VRRP also support a number of routers to form a virtual group which acts like … [Read more...] about VRRP Configuration(virtual router redundancy protocol)