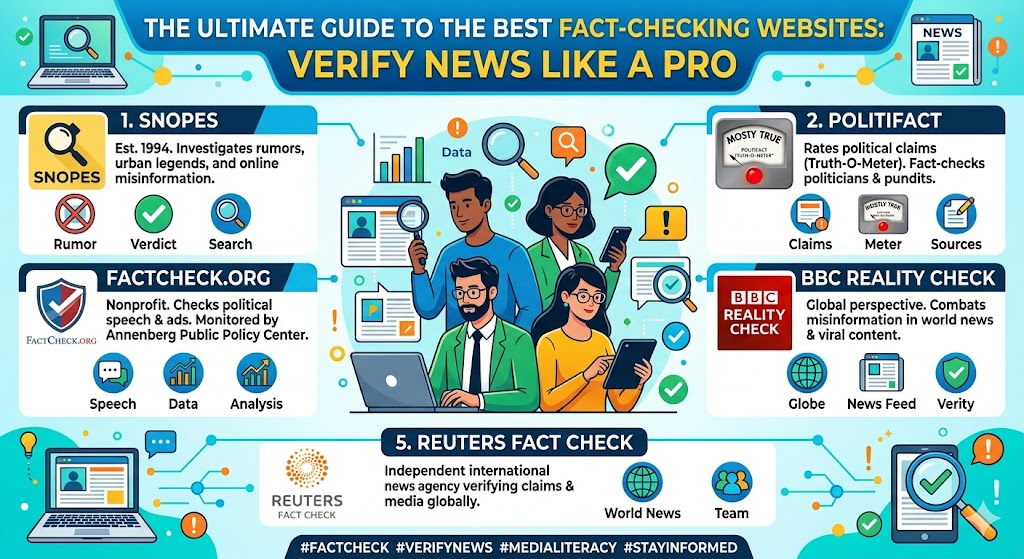
The top sites for verifying news or any misleading information are independent fact-checking organizations that investigate claims, viral stories, rumors, and political statements using transparent methods, original sources, and corrections when needed. Many adhere to the International Fact-Checking Network (IFCN) Code of Principles, a global standard for nonpartisanship, … [Read more...] about The Ultimate Guide to the Best Fact-Checking Websites: Verify News Like a Pro
Internet Security and Safety
NIST Incident Response Phases Explained-Special Publication (SP) 800-61 Revision 3
The NIST incident response lifecycle has evolved over time. In the latest guidance from NIST Special Publication (SP) 800-61 Revision 3 (published in 2025), it is integrated with the NIST Cybersecurity Framework (CSF) 2.0 to emphasize a continuous, risk-management-oriented approach rather than a strictly linear process. This contrasts with the previous Revision 2 model, which … [Read more...] about NIST Incident Response Phases Explained-Special Publication (SP) 800-61 Revision 3
UK’s Digital Guardians: The Key Organizations Watching Over Social Media Content
There are several organizations in the UK that monitor social media content, primarily for regulatory, safety, or enforcement purposes related to harmful, illegal, or misleading material. These include government regulators, charities, and law enforcement bodies.You will usefel contents and guidance in those organizaiton's website and can contact for help or guidance. Here's a … [Read more...] about UK’s Digital Guardians: The Key Organizations Watching Over Social Media Content
Online Abuse vs. Harassment: Know the Signs & Differences
The rise of the internet and social media has transformed how we connect, but it has also given rise to darker behaviors like online abuse and harassment. These terms are often used interchangeably, yet they represent distinct forms of harm in the digital space. Both can leave lasting emotional and psychological scars, but they differ in their nature, intent, and execution. … [Read more...] about Online Abuse vs. Harassment: Know the Signs & Differences
The Silent War on Free Speech: How Discourse is Controlled and Manipulated
The concept of a "monopoly on discourse" refers to a situation where one or a few entities control or dominate the public conversation, shaping narratives, setting agendas, and potentially marginalizing alternative viewpoints. Here's a breakdown of this phenomenon: … [Read more...] about The Silent War on Free Speech: How Discourse is Controlled and Manipulated
Exploring Freedom of Speech: Principles, Challenges, and Global Perspectives
Freedom of speech is a fundamental principle that allows individuals to express their opinions, ideas, and information without fear of censorship or retaliation from the government. Here's a comprehensive overview: Definition and Importance: Definition: Freedom of speech generally includes the right to express information, ideas, and opinions through speech, writing, art, … [Read more...] about Exploring Freedom of Speech: Principles, Challenges, and Global Perspectives
Master User Empowerment: Learn and Apply Proven Techniques
User empowerment is a concept that revolves around giving individuals the tools, resources, knowledge, and confidence they need to take control of their lives, make informed decisions, and advocate for themselves. Here's how user empowerment can be understood and implemented: Key Aspects of User Empowerment: Access to Information: Education: Providing educational … [Read more...] about Master User Empowerment: Learn and Apply Proven Techniques
Big Tech on Trial: Are Social Media Owners Above the Law?
The accountability of social media owners is a complex and multifaceted issue that involves legal, ethical, and regulatory considerations. Here's an overview based on current discussions and developments: Legal Accountability: In many jurisdictions, social media platforms have been largely shielded by laws like Section 230 of the Communications Decency Act in the United … [Read more...] about Big Tech on Trial: Are Social Media Owners Above the Law?
Should Billionaires Control Social Media?
The Dilemma of Social Media Control: A Handful of Businessmen Swaying Public Opinion In the digital age, social media has transcended its role as a mere platform for social interaction to become a pivotal force in shaping public discourse, political landscapes, and cultural trends. However, this power is largely centralized in the hands of a few major companies, controlled by … [Read more...] about Should Billionaires Control Social Media?
Election Manipulation: Social Media’s Growing Role
The advent of social media has revolutionized how political campaigns are conducted, how information is disseminated, and how voters engage with electoral processes. However, this digital transformation has brought with it significant challenges concerning the management of political speech, the spread of misinformation, and the potential for foreign influence in elections. … [Read more...] about Election Manipulation: Social Media’s Growing Role
Online Anonymity: Shield for Free Speech or Cover for Crime?
Anonymity Online: Protection or Problem? The concept of anonymity online has become a cornerstone of digital culture, offering a double-edged sword that cuts through both the realms of free speech and digital security. Anonymity has been lauded for its protection of privacy and free expression, yet it has also been criticized for enabling cybercrime, harassment, and the spread … [Read more...] about Online Anonymity: Shield for Free Speech or Cover for Crime?
Government Spying vs. Privacy: What You Need to Know
Surveillance and Security vs. Privacy Rights: Navigating the Ethical and Legal Labyrinth The debate over government access to user data for security purposes versus the protection of individual privacy rights has been one of the most contentious issues in modern society, particularly with the advent of digital communication and data storage. This discussion becomes even more … [Read more...] about Government Spying vs. Privacy: What You Need to Know
How Different Countries’ Data Rules Impact Your Favorite Platforms
In the digital age, where data is often considered the new oil, the concept of data sovereignty has emerged as a critical element in the global regulatory landscape. Data sovereignty refers to the notion that data is subject to the laws of the country in which it is collected, stored, or processed. This principle has profound implications for global platforms that operate … [Read more...] about How Different Countries’ Data Rules Impact Your Favorite Platforms
The Illusion of Consent: How Privacy Policies Fail to Safeguard Users
In an era where digital interactions define much of our daily lives, privacy has become a commodity, often traded away under the guise of consent through privacy policies. These documents, intended to safeguard user data and privacy, frequently fall short, creating an illusion of consent that does little to protect individuals. This article delves into why privacy policies … [Read more...] about The Illusion of Consent: How Privacy Policies Fail to Safeguard Users
The Algorithm Effect: Who’s Really Controlling Public Opinion?
The Role of Algorithms in Shaping Public Opinion In the digital age, algorithms have become the silent architects of our informational environment. They curate, filter, and prioritize content across social media platforms, search engines, and news aggregators, profoundly influencing what we learn, believe, and discuss. This article delves into how algorithms shape public … [Read more...] about The Algorithm Effect: Who’s Really Controlling Public Opinion?
Can Free Speech Thrive in a Moderated World?
Balancing Free Speech and Content Moderation: A Modern Dilemma The digital age has transformed the landscape of free speech, expanding its boundaries while simultaneously introducing complex challenges in content moderation. With the rise of social media platforms, the internet has become a global stage where ideas, opinions, and content are shared at unprecedented speeds. … [Read more...] about Can Free Speech Thrive in a Moderated World?
Social Media at a Crossroads: Regulation vs. Self-Regulation
The rise of social media has transformed communication, commerce, and culture, bringing with it unprecedented opportunities and challenges. As platforms like X, Instagram, and TikTok continue to grow, the debate intensifies over whether these entities should be regulated by governments or if they should govern themselves through self-regulation. This article delves into the … [Read more...] about Social Media at a Crossroads: Regulation vs. Self-Regulation
Online Safety Revolution: Understanding the UK’s Landmark Act
Navigating the UK's Online Safety Act 2023: A Comprehensive Overview The United Kingdom's Online Safety Act 2023, a landmark piece of legislation, marks a significant shift in the regulation of online platforms, aiming to create a safer digital environment for UK users. Here's an in-depth look at what the Act entails, its implications, and the ongoing debate surrounding its … [Read more...] about Online Safety Revolution: Understanding the UK’s Landmark Act
Unveiling the PACT Act: A New Dawn for Internet Transparency and Accountability
In the digital age, where the internet serves as a global agora for communication, commerce, and contention, the governance of online platforms has become a matter of significant public interest. Enter the Platform Accountability and Consumer Transparency Act (PACT Act), a legislative effort aimed at reshaping how internet platforms manage content, respect user rights, and … [Read more...] about Unveiling the PACT Act: A New Dawn for Internet Transparency and Accountability