In today’s cyber security, landscape database is considered to be the most important asset of an organization, which holds sensitive information about the business and employees . Having installed and configured firewalls, IDS and end point security, one should not expect that the database is secure and there is no way anyone can breach data. Most of the major data breach … [Read more...] about 20 Types of Database Security to Defend Against Data Breach
database
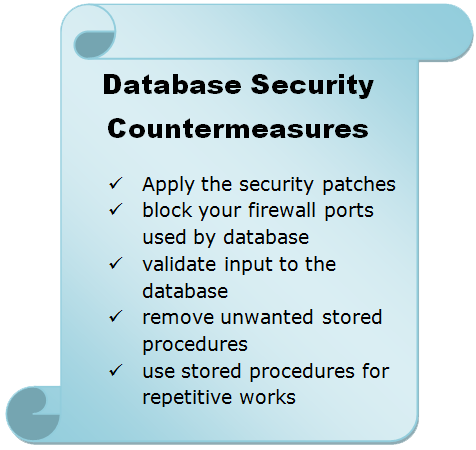
Database Security Issues and Countermeasures
One of the least prioritize part in data base security is not taking countermeasures against database access. Some solid measures that you can take to secure the access methods in your database are: Whether you use Oracle database or Microsoft SQL database, both the organization releases their security patch almost regular basis. So, make sure that you visit the security … [Read more...] about Database Security Issues and Countermeasures
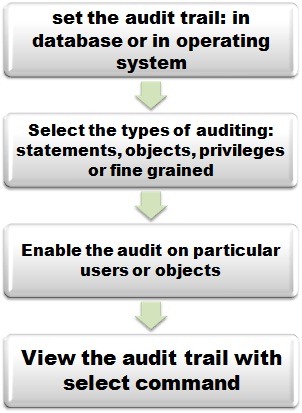
Oracle Audit Setting Commands
An auditor needs to check the Oracle database in order to gather some useful and important information to conduct his audit. In fact, an auditor will ask the system administrator to run the commands and collect the information on behalf of him. The following are the basic commands that you need to know before starting the proper audit of the audit trail. To get a list of all … [Read more...] about Oracle Audit Setting Commands
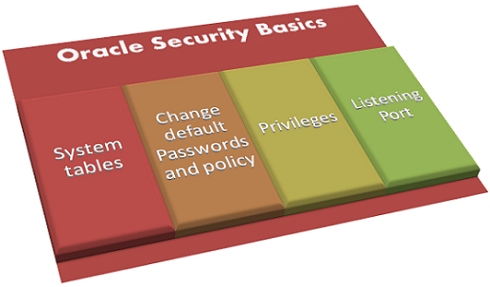
Oracle Security Basics
Popularity has a price to pay since everything on this world has its face value. And Oracle database software is no different than that. In this post, you may expect to have some basic idea on Oracle security and its risks. The features of Oracle that has security risks are: System tables Passwords Privileges Oracle Listener … [Read more...] about Oracle Security Basics
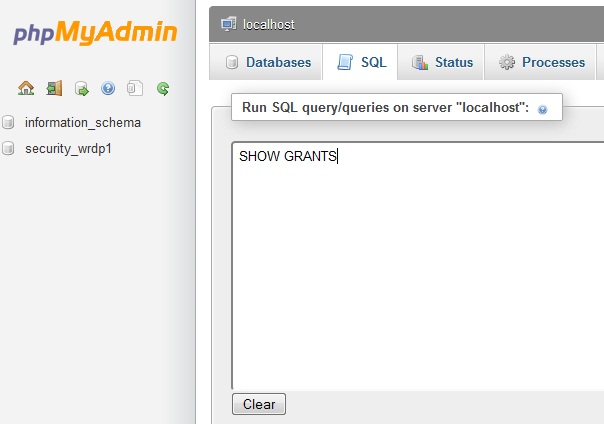
MySQL Security Settings Checklist and Issues
Securing MySQL requires not only hardening the security configuration of your database itself but also the web server along with the operating system. As you know that most of the web hosting provider love Linux and Apache as part of their web-hosting solution, you need to make sure that your host is taking proper security measures to ensure tighter control of Apache and OS. … [Read more...] about MySQL Security Settings Checklist and Issues
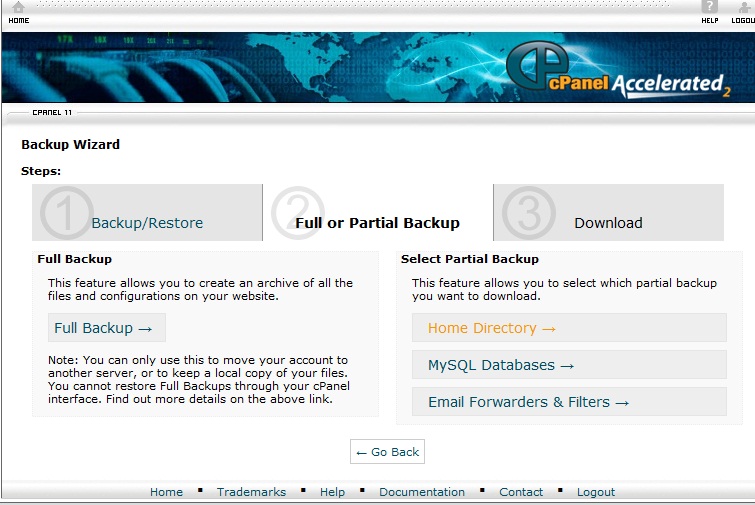
WordPress Backup & Restore:Database and Home Directory
There are thousands of wordpress experts who will suggest the beginners to take regular backup of their websites. If you are just learning how to make wordpress blog, then you may not pay attention to the importance of taking backup and restoration. Think about this you have a blog of 50 articles and getting 1000 organic traffic and one day morning when you logon to your … [Read more...] about WordPress Backup & Restore:Database and Home Directory