Popularity has a price to pay since everything on this world has its face value. And Oracle database software is no different than that. In this post, you may expect to have some basic idea on Oracle security and its risks. The features of Oracle that has security risks are:
- System tables
- Passwords
- Privileges
- Oracle Listener
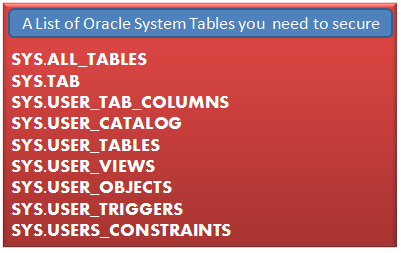
System Tables:as you know that the heart of the database is its table, which servers the main purpose of a database-storing data. The most important tables to protect are the systems tables such as SYS.USER_TABLES, SYS.USER_VIEWS, SYS.USER_OBJECTS, SYS.USER_TRIGGERS , SYS.USERS_CONSTRAINTS etc.
As an information security professional, you need to assume that all these tables are secured and you need to audit Oracle security and privileges roles to make sure the privacy of the data. If you Oracle database are hosted in a Windows system, you can sue Oracle audit tool in order to automate the security checking process and you can find such tool at Oracle audit tool page of cqure.net site .
Passwords: After installing Oracle, you need to change the default password of Oracle, in addition to changing passwords; you can implement a strong password policy such as enforcing minimal length, complexity, lockout, expiration and avoiding reuse of passwords.
Privileges: Oracle has several types of privileges including system and object privileges, which are basically used to allow certain users to access certain objects in a database (for example tables are objects). You need to look out for misconfigured privileges in order to prevent unauthorized or unwanted persons from viewing you sensitive data.
Oracle Listener: the purpose of the listener service is to receive users’ requests and transfer them to the requested database. By default, Oracle use TCP port 1521 as a listening port. An Oracle administrator must need to change this port so as an attacker cannot make any easy guess. Remember that the listener is the first point of entry to a database and if it is not secured, it can reveal sensitive information about your database and the host operating system.
So, the basic steps you can take to make Oracle secure from its well-known vulnerabilities and threats are to change the listening port, audit the system tables and check the privilege levels for each users