Almost every Internet user has their home network that every family member use to Internet access.For your home network security you can follow a few simple steps to eliminate the chances of your network being compromised. Before diving deep into the home network security issues, you may have a look at the vulnerability points in your network, including your client machine. … [Read more...] about 20 Ways to Secure Home Network
router
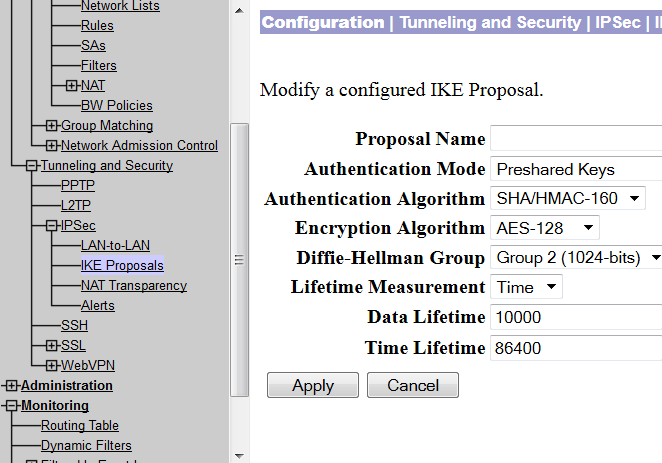
Site to Site VPN Between Cisco VPN Concentrator and Router
At times, it is economical to build a VPN tunnel with the available networking resources. For example, if you have a VPN concentrator and you need to connect a small office securely with your network, you can do so by installing a low priced Cisco router in the remote office. This post will demonstrate how you can build VPN using a VPN concentrator and a Cisco router. … [Read more...] about Site to Site VPN Between Cisco VPN Concentrator and Router
Cisco Router Security Check for Auditor
Since router is the key to access an organization's network from the outside world, the maximum security priority should be given to routers that are connected to the Internet and to the important application servers. ISO-27001 has already defined standard router security checklist, which any organization can use to improve their router securities. This post aims to … [Read more...] about Cisco Router Security Check for Auditor
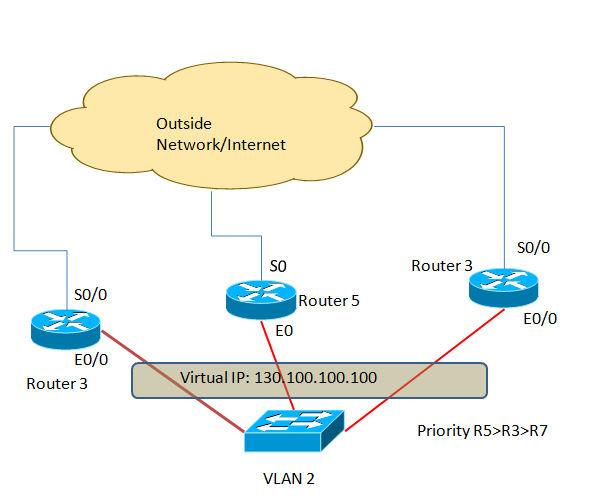
HSRP Configuration(Hot Standby Routing Protocol)
HSRP or hot standby routing protocol provides network redundancy solutions to routers.By configuring HSRP in a number of routers in a network you can offer your customers the opportunity to enjoy seamless network or Internet access opportunity. HSRP is mainly used in the perimeter network or in a network where high-available is a must or has zero tolerance to network downtime. … [Read more...] about HSRP Configuration(Hot Standby Routing Protocol)
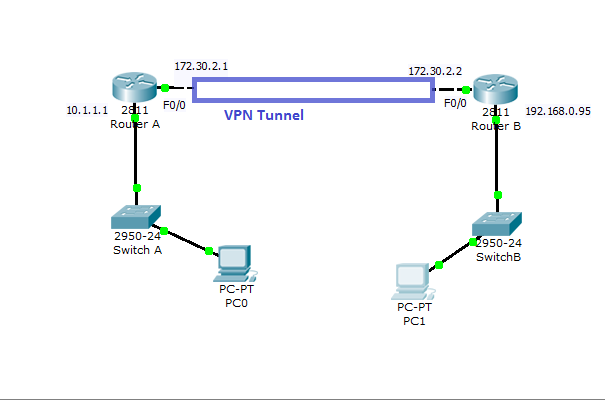
Cisco VPN Configuration in IOS Routers
How to Configure VPN in Cisco Routers Virtual private network can be configured with most of the Cisco routers( 800 to 7500 series) with IOS version 12 or higher.VPN can be implemented in a number of ways--with various level of security measures and configuration. To determine the right VPN configuration for your network, you need to have a solid understanding in cryptographic … [Read more...] about Cisco VPN Configuration in IOS Routers
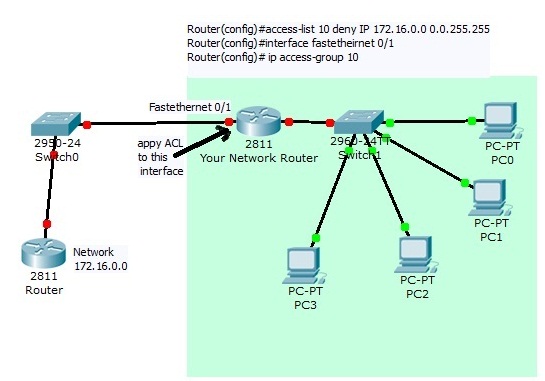
Access Control List Configuration on Cisco Router
What is ACL: Access control list or ACLs are a set of if-then rules set on a router to allow or deny a specific group of IP to send or receive traffic from your network into another network. When you apply an ACL to a route interface for incoming traffic then every incoming packets will be compared with your ACL first, if a match is found then either permit or deny action … [Read more...] about Access Control List Configuration on Cisco Router
Screening Router Security Test
Much small-scale business does not use firewall as their first line of defense any web attacks to their internal network. Instead, they use a router between the Internet and Internal network to control incoming and outgoing traffic flow- this type of use of router is known as screening router. In fact, configuring ACLs inside a router can be a viable and effective solution … [Read more...] about Screening Router Security Test