VRRP or virtual router redundancy protocol provides router or switch interfaces failover and failback facility for seamless operation of a network. VRRP almost similar to HSRP in terms of operations and functions, but with a few added features such as VRRP supports up to 255 groups. Just like HSRP, VRRP also support a number of routers to form a virtual group which acts like … [Read more...] about VRRP Configuration(virtual router redundancy protocol)
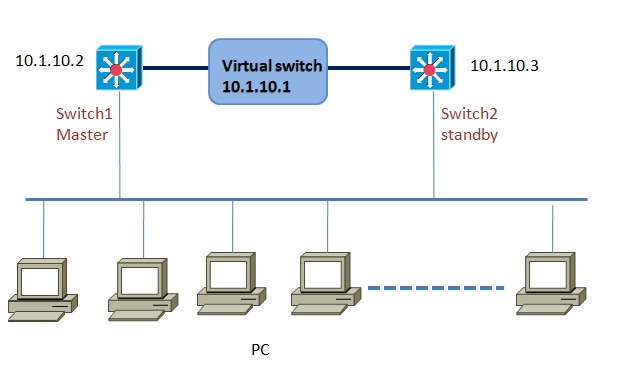
hsrp
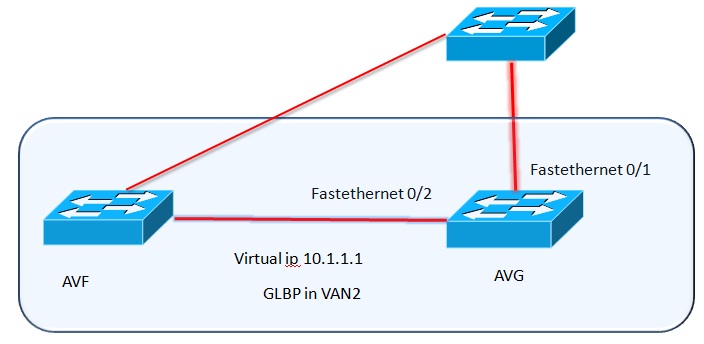
GLBP-Gateway Load Balancing Protocol Configuration
What is GLBP: Gateway Load balancing protocol is a Cisco proprietary protocol for both redundancy and load balancing in Cisco switches and routers. Although VRRP or HSRP provides a network link redundancy to router traffic in a or a number of routers in case of failure to the main active routes, but they do not allow to fully utilizing the available network resources. GLBP … [Read more...] about GLBP-Gateway Load Balancing Protocol Configuration
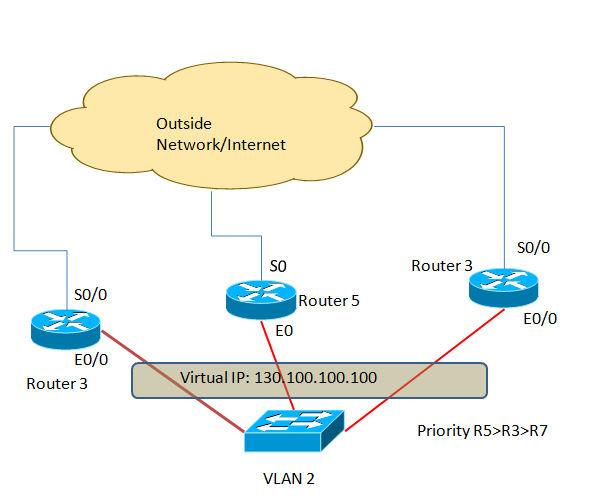
HSRP Configuration(Hot Standby Routing Protocol)
HSRP or hot standby routing protocol provides network redundancy solutions to routers.By configuring HSRP in a number of routers in a network you can offer your customers the opportunity to enjoy seamless network or Internet access opportunity. HSRP is mainly used in the perimeter network or in a network where high-available is a must or has zero tolerance to network downtime. … [Read more...] about HSRP Configuration(Hot Standby Routing Protocol)