Acunetix web vulnerability scanner help to find vulnerability in a website so as you can make your site or blog as secure as possible. Acunetix has a free version that you can use to find some of the common vulnerabilities of a website.In this article I will show you how you can use the free version of acunetix to figure out how much secure you blog is.Although Acunetix has a robust web vulnerability scanner that is capable of give you a detail report of your website’s security loopholes, you can use their free version to learn about this software if you are a new to the blogging world.
Why you need to check your website’s vulnerability?
whether you have a blog or a website, you are always look out for discovering your website’s vulnerability so as you do not have to face untoward situation which not only cause havoc to your online business but also can cause you lost your reputation as a business owner. In reality no website is vulnerability proof and most of the prolific web brand were at least once under attack in their life time in the world wider web.
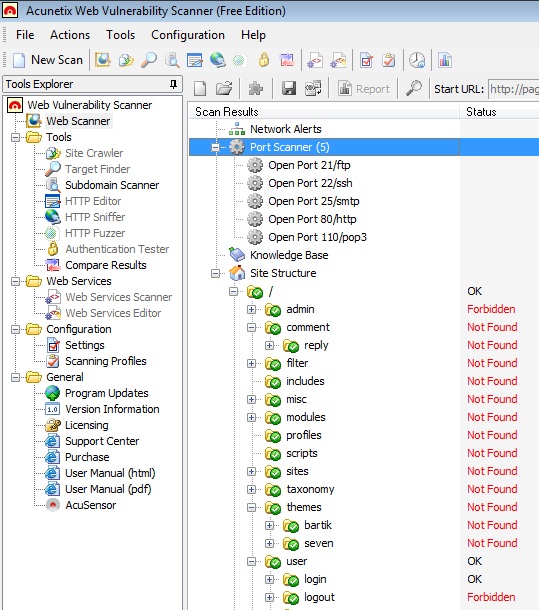
By looking at the features of the is software you may fee that running acunetix is very simple, which is very true, even a beginner level webmaster can run it, but you need to know a bit about web protocols and coding vulnerabilities before you can read the report generated by this scanner.Since I will only assume that you already have some basic knowledge about web vulnerabilities, you should be able to find the following vulnerabilities in the report”
- Web alerts
- Network Alerts
- Port Scanner
- Site Structure
If you’ve just started learning about web security and want to scan your own blog, then I would suggest you to learn about basics of TCP/IP protocol, HTML coding and web site structures before you run this vulnerability scanner.You can download the trial version of Acunetix at http://www.acunetix.com/vulnerability-scanner/
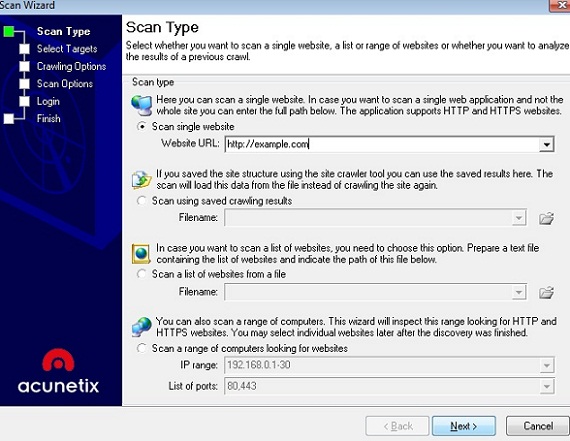
After downloading and installing this software you need to start the software and then type the URL of your blog in the Website URL box of the “scan type” option. When you want to stop your scan you can do so by clicking the stop icon on the top-right of your scanner.I would recommend the new blogger to use the trial version of Acunetix in they are really interested to learn about web security.