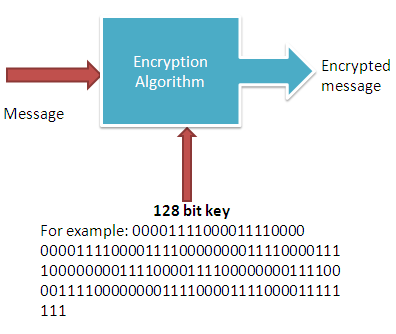
The purpose of any cryptography is to ensure the confidentiality, authenticity, non-repudiation and integrity of the data. And all these goals are achieved with the use of cryptography keys. The 128 bit key is such a type of key that ensure all the intended objectives of using a crypto-system or cryptographic algorithm.it is the key which needs to be secret in order to keep information private.
128 is the length of the key.
A message is called plain text before it gets encrypted with a key. The length of the key is determined by the algorithm. A key is basically a binary number from 0 to n. The length of the key is 2n. For example if you choose a 128 bit key, then you can say that your key will be any number between 0 to 2128. In other words, your key length can be anything between 128 0s to 128 1s. Remember that higher the length of the key, the better your message is protected.
The higher the length the better
The strength of the key depends on its length. Keys with longer length (128 bit or above) are almost unbreakable since it takes several to couple of hundred years to break them with the modern computing system. But with length comes the complexity of encoding and decoding. That is why messages with long keys take more time to encode and decode than the keys with shorter length.
What is the ideal length of the key?
There is no straight forward answer. It depends on the situation. Depending on the sensitivity and criticality of data, you can categories them as minor, major and critical resources. Since critical data are more sensitive and valuable, you can encrypt them with longer keys such as 128 or higher.
The importance of the key
In the earlier days of cryptography the encryption algorithm was kept secret. Only the sender and the receiver used to know about it. On the contrary, the modern cryptosystem do not depend on the secrecy of its algorithm. Instead they rely on the keys. In order to keep the message confidential, the keys must be kept secret. As you already know that the power of decryption of a message entirely depends on the processing power of a computer. Since the computing power is increasing and faster computing is becoming available to the people, it has become increasingly important to choose a longer key. In the early 90s, the 56 bit key was thought to be sufficiently safe. But with the advent of supercomputing, the 56 bit key is no longer considered safe. The 128 bit key is the minimum length you need to keep in mind when you want to protect your data from prying eyes.
Example of a 128 bit keys:
11110000111100001100 11110000111100001100 11110000111100001100 11111111111111111111 00000000000000001111 00000000000011111111 0001111
Remember that the total number of 1s or 0s should be 128 in a 128 bit key. It does not matter if you are using symmetric key system or asymmetric key (public key system) system, the strength of your crypto-system depends on the length of the key and the higher the length the better the security.