The purpose of the Linux security checklist is to help the Linux users, entry-level, to become familiar with the most common security vulnerability of Linux operations systems. As you know security checking needs to be verified against well established practices, the following steps are necessary to following before starting your Linux security checking. Version number of … [Read more...] about Linux Security Basics
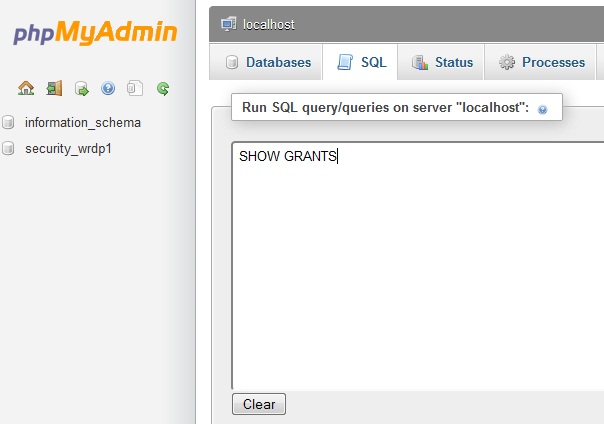
MySQL Security Settings Checklist and Issues
Securing MySQL requires not only hardening the security configuration of your database itself but also the web server along with the operating system. As you know that most of the web hosting provider love Linux and Apache as part of their web-hosting solution, you need to make sure that your host is taking proper security measures to ensure tighter control of Apache and OS. … [Read more...] about MySQL Security Settings Checklist and Issues
Quality Control Leaders’ Thoughts
Sustainable growth of a company is not any easy task and it is a clear indicative of a company’s objective of continuous quality control. In today’s world we see that there are only a handful number of companies that stand out others with their product. Why only a few company is making billions when some are thinking about closing down a product’s life cycle or even closing … [Read more...] about Quality Control Leaders’ Thoughts
CMS Planning : WordPress Vs Drupal Vs Joomla
Building a website or blog with CMS such as Wordpress, Joomla or Drupal seems quite easy and requires only a few clicks on your host panel to bring your site online. What is the most important factor when you build a CMS based site is that you need a long term plan for the growth and expandability in terms of users, features, web space or even hosting. Let’s take a look at what … [Read more...] about CMS Planning : WordPress Vs Drupal Vs Joomla
Physical Security of Information Assets
Without paying proper attention to the physical security of information asset your IT assets and infrastructure are always under security threats from known or unknown sources or from accidental hazards. An IT security manager or designer will always need to pay equal or even more attention to ensure that his all the information assets are physically secured. It is not … [Read more...] about Physical Security of Information Assets
Project Manager Interview Questions and Answers
This article will show you a few but the most important sample questions and answers that a project manager may face in an interview.Please read all the questions carefully and prepare your own version of the answers depending on what kind or type of projects you already have completed. Q: Please describe a project that you undertaken? I have the opportunity to … [Read more...] about Project Manager Interview Questions and Answers
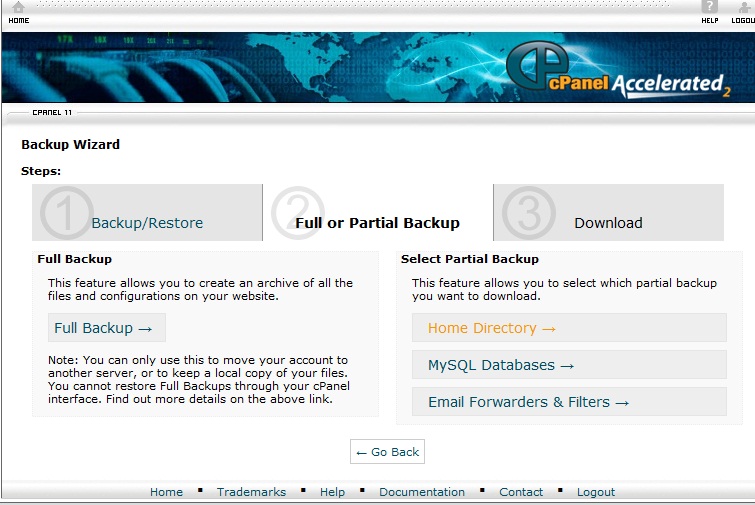
WordPress Backup & Restore:Database and Home Directory
There are thousands of wordpress experts who will suggest the beginners to take regular backup of their websites. If you are just learning how to make wordpress blog, then you may not pay attention to the importance of taking backup and restoration. Think about this you have a blog of 50 articles and getting 1000 organic traffic and one day morning when you logon to your … [Read more...] about WordPress Backup & Restore:Database and Home Directory
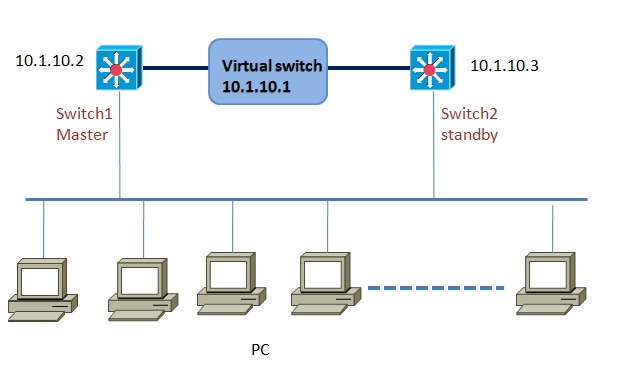
VRRP Configuration(virtual router redundancy protocol)
VRRP or virtual router redundancy protocol provides router or switch interfaces failover and failback facility for seamless operation of a network. VRRP almost similar to HSRP in terms of operations and functions, but with a few added features such as VRRP supports up to 255 groups. Just like HSRP, VRRP also support a number of routers to form a virtual group which acts like … [Read more...] about VRRP Configuration(virtual router redundancy protocol)
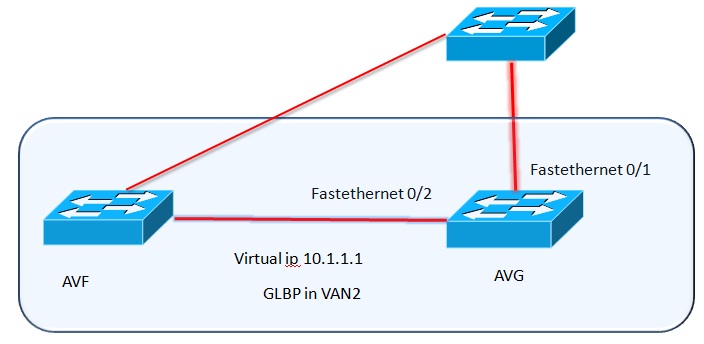
GLBP-Gateway Load Balancing Protocol Configuration
What is GLBP: Gateway Load balancing protocol is a Cisco proprietary protocol for both redundancy and load balancing in Cisco switches and routers. Although VRRP or HSRP provides a network link redundancy to router traffic in a or a number of routers in case of failure to the main active routes, but they do not allow to fully utilizing the available network resources. GLBP … [Read more...] about GLBP-Gateway Load Balancing Protocol Configuration
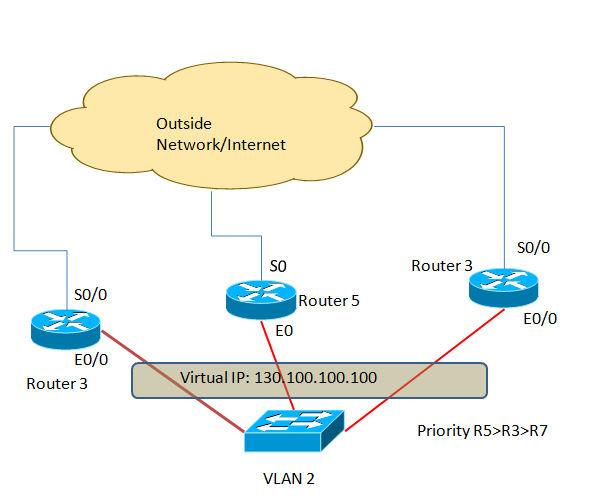
HSRP Configuration(Hot Standby Routing Protocol)
HSRP or hot standby routing protocol provides network redundancy solutions to routers.By configuring HSRP in a number of routers in a network you can offer your customers the opportunity to enjoy seamless network or Internet access opportunity. HSRP is mainly used in the perimeter network or in a network where high-available is a must or has zero tolerance to network downtime. … [Read more...] about HSRP Configuration(Hot Standby Routing Protocol)
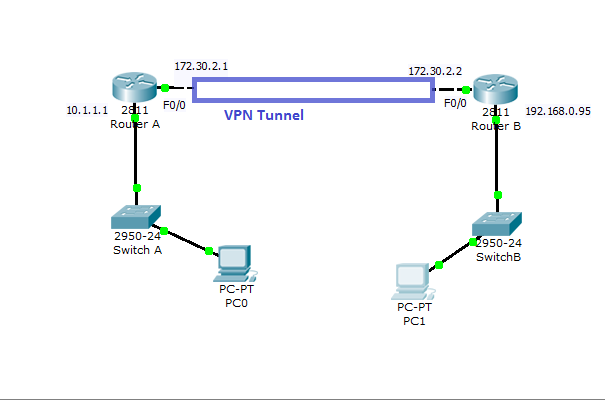
Cisco VPN Configuration in IOS Routers
How to Configure VPN in Cisco Routers Virtual private network can be configured with most of the Cisco routers( 800 to 7500 series) with IOS version 12 or higher.VPN can be implemented in a number of ways--with various level of security measures and configuration. To determine the right VPN configuration for your network, you need to have a solid understanding in cryptographic … [Read more...] about Cisco VPN Configuration in IOS Routers