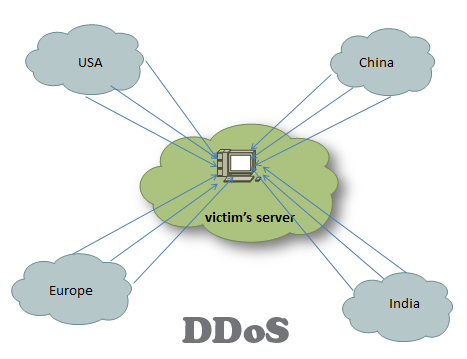
Despite the differences in the mechanism, the purpose of the DDoS (distributed denial of service attack) is the same- to deplete the resources on the victim’s network. DDoS can be broadly divided into two types: bandwidth depletion and resource depletion. This post aims to give you a broad overview of the various types of DDoS attacks and their prevention techniques. … [Read more...] about 10 Major Types of DDoS Attacks and Prevention
ddos
15 Ways to Stop DDoS Attacks in your Network
To stop DDoS (distributed denial of service) attack, one needs to have a clear understanding of what happens when an attack takes place. In short, a DDoS attack can be accomplished by exploiting vulnerabilities in the server or by consuming server resources (for example, memory, hard disk, and so forth). … [Read more...] about 15 Ways to Stop DDoS Attacks in your Network