FTP or file transfer protocol is used to transfer files between two computers: one is FTP host or server and another is FTP client. In addition to transferring files, FTP helps to gain access to the physical location of the server to modify files such as file deleting, folder creating or even modifying file contents.
Before knowing the difference between active and passive FTP, you need to know how FTP functions. Normally, when you open FTP connectivity with a FTP server, there opens two connections between the computers: one is used to transfer data and another one is used to transfer control signals. Both the channels are TCP connections. For commands, TCP port number 21 is used and the port number 20 is used for data.
Benefit of active FTP: it increase FTP server security
Benefit of passive FTP: it requires less configuration changes on client computer.
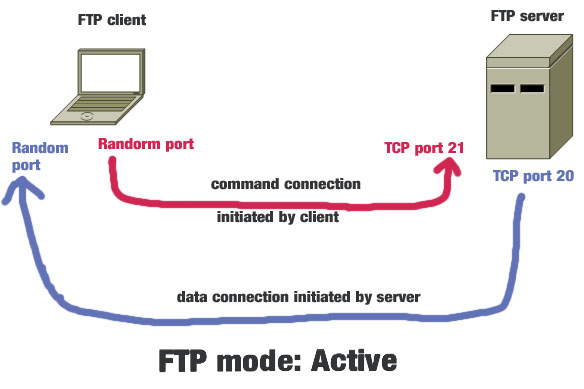
Active mode
In this mode a FTP client machine opens a connection using a random port to the server’s port 21. Then server opens a data port with its port number 20 to a random port of the client machine. The data port number in the client machine is supplied by the client machine. Both the servers and the clients are responsible for opening connection. The client starts the command channel connection whereas the server start the data channel connection. When configuring FTP active mode you need to make sure the ports are open in the client machines, if you are using a firewall.
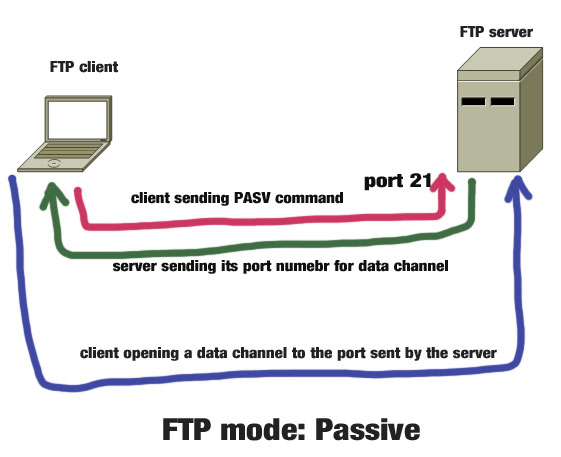
Passive mode
In passive mode both the command and data channel is opened by the client machine. At the starting phase of the connection, the client opens a TCP connection from a random port to the server’s port 21.next the client send a PASV command to the server and the server sends the port number that it wants to use as a data channel. Then, the client sends data the port number send by the server. The port number supplied by the server for data channel must be opened in the server side firewall. In IIS, there is an option to choose a range of ports to be used for data channel. After defining the range of ports, you need to open that port range in the server firewall. The port number used by the clinet in passive mode are always greater than 1023.
In active mode, the server use well known port 20 for data and port 21 for command, whereas the client uses random port numbers for both data and command.
Which mode is more secure? Both the mode is insecure because they do not use SSL. Therefore, anybody sniffing the network card can read the data pass through FTP (both in active and passive modes)