There can be various reasons why hackers want to gain access to your account. Once they gain access to your Gmail account, hackers can use it for various purpose and they post aims to help you secure Gmail account so that you can regain access to your Gmail even if your account password get compromised.
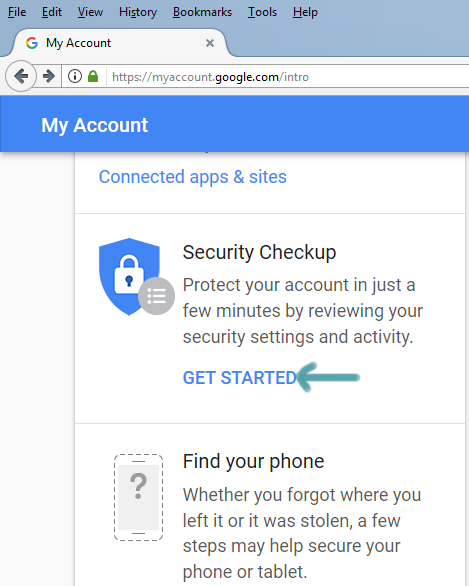
Step 1: setup recover phone and recovery email address
The easiest way to get started with Gmail security is to visit https://myaccount.google.com and then click on “Get Started” under security check-up.
Next, click on ‘ sign’ in to start’ and add recover phone and recovery email address and save it. In case your account gets stolen you can use these two options to get back your account.
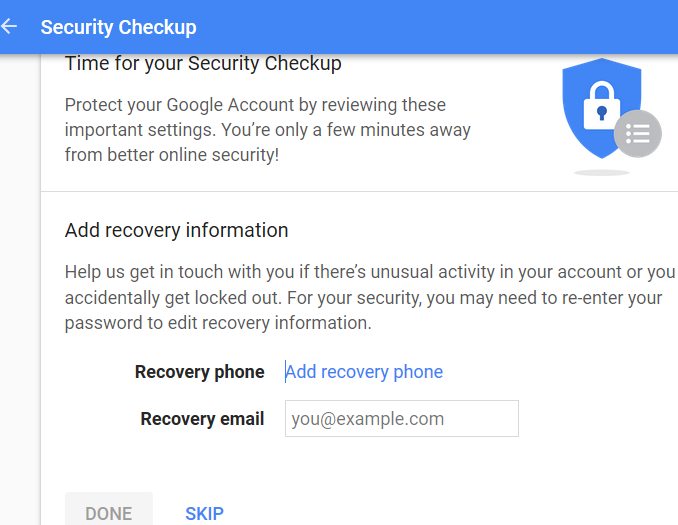
Remember that Google has decided to discontinue to get rid of the account security questions. So, if you already have the security questions setup for your account, you can delete that option from this security check-up page. If you have never setup security questions, then you will not see remove security questions options.
Step 2: Enable 2 step verification code
Log in to your Gmail account and click on the small cog icon on the top right.
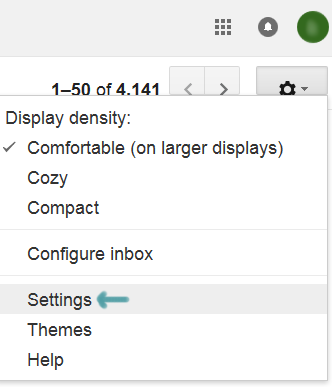
Next click on “account and import” and then click on “change password recovery options” under “Change account settings:” section.
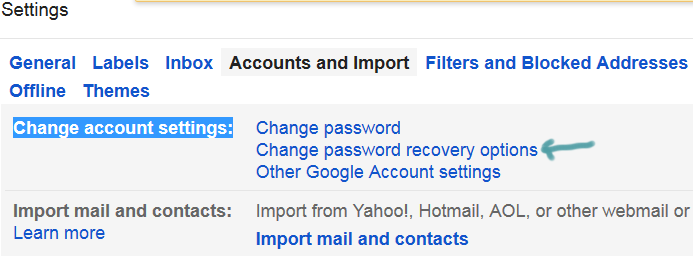
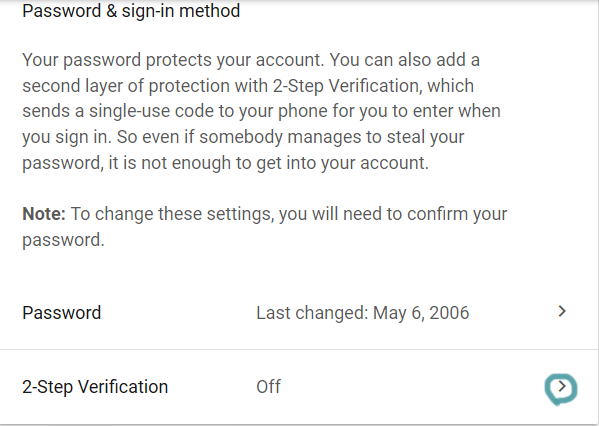
Scroll down and click on “2-Step verification” under “ sign in to Google”.
A new window will appear and click on “get started”.
Enter your email password to access the setup page. Next, type your phone number and select either ‘text message’ or ‘phone call’ to receive your access code.
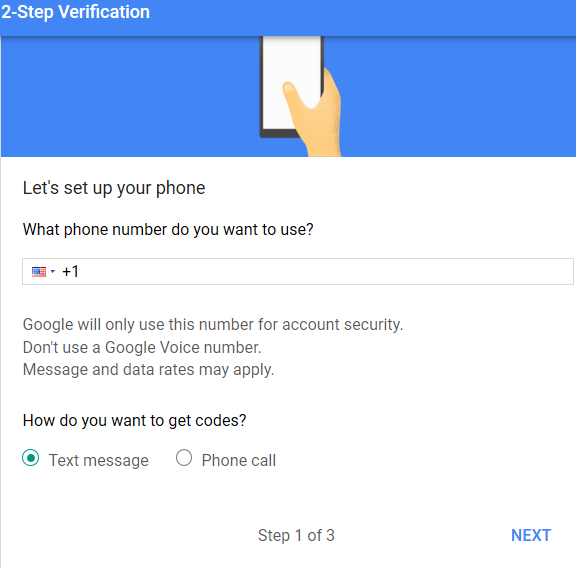
Click ‘Next’ and enter the 6-digit access code that you received on your phone in order to turn on the two-step verification method. If everything goes well, you will see the ‘verified’ message just beside your phone number.
Step 3: setup a complex password
Though it sounds a bit cliché, the reality is that your Gmail account password is the key to unlock your mailbox. When setup your password use a strong, long and not-easily-guessable password to make it harder for anyone to try to gain access to your account based on your social profile information.
Finally, since the success of two-step authentication depends on the security of your mobile as well, you need to make sure that your mobile device is also password protected. Remember to tighten the security of your recovery email address as well because it may be also used by the hacker to gain access to your Gmail.
