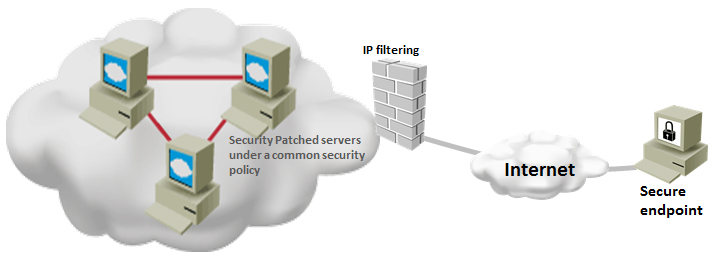
By following windows server security best practices, you can ensure that your server is running under the minimum required security settings. Implementing security best practices does not mean that your systems do not have any vulnerability. But, it gives a sense of security that your system will not be easily compromised and it least will perform better when it has to fight … [Read more...] about Top 20 Windows Server Security Hardening Best Practices
windows
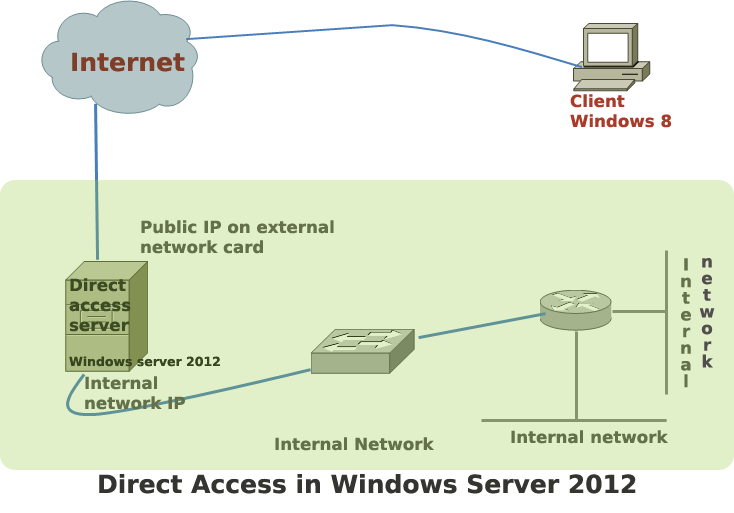
Steps to Configure Direct Access in Windows Server 2012
Direct access is the commercial name of Windows 2012 server’s remote access solution. In earlier versions of Windows, remote access offered limited features to the remote users. Windows 2012 is the first Microsoft server that makes remote access users feel like working within the corporate network. … [Read more...] about Steps to Configure Direct Access in Windows Server 2012
20 Forensic Investigation Tools for Windows
To investigate Windows system security breach for any potential security breach, investigators need to collect forensic evidence. Microsoft has developed a number of free tools that any security investigator can use for his forensic analysis. This post will give you a list of easy-to-use and free forensic tools, include a few command line utilities and commands. … [Read more...] about 20 Forensic Investigation Tools for Windows
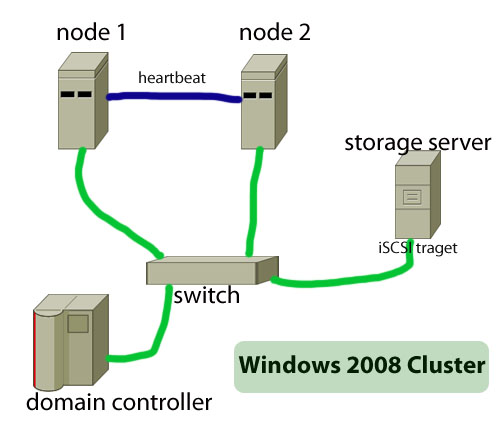
How to Build Failover Cluster in Windows Server 2008
The main objective of a failover cluster is to ensure high availability of services. A failover cluster means that only one server--which is also known as active server--in the cluster will provide the service such as a file server or webserver. When this active server will go offline or will be out of service, another server in the cluster will provide the same service, … [Read more...] about How to Build Failover Cluster in Windows Server 2008
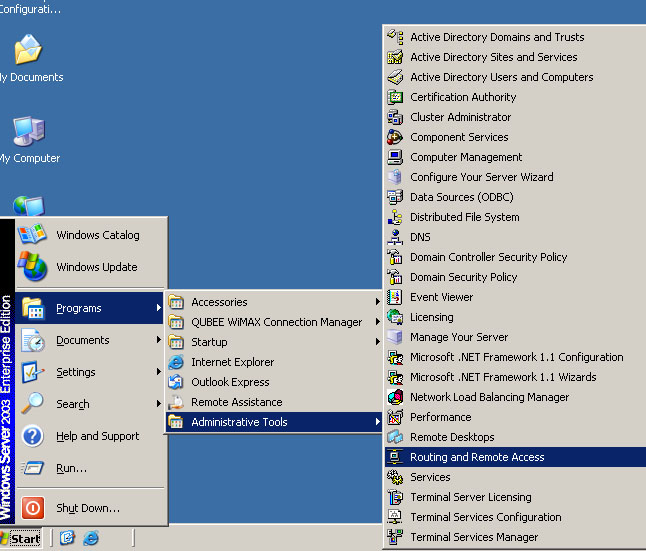
How to Configure VPN,RAS and IPSec Policy in Windows Server
VPN is a trusted and secure network, which use tunneling and protocol(PPTP,L2TPIPSec) to make data transmission through the public network. RAS: remote access service used to access server remotely from client terminal using dial-up connection. IAS:Internet authentication service is used to remotely and centrally manage all RAS server and keep remote access policy … [Read more...] about How to Configure VPN,RAS and IPSec Policy in Windows Server
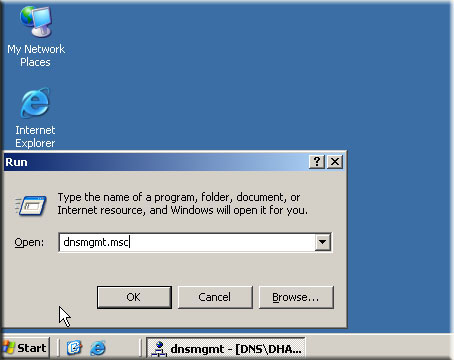
Windows DNS Server Configuration
DNS or domain name system is one of the most important parts of client-server model. Without a DNS no client could be part of a domain and there will be no way you can convert domain name into the IP address of the server. In this post you will find basic procedures that you can use to configure DNS for your domain controller. Though the procedures described in this post is … [Read more...] about Windows DNS Server Configuration
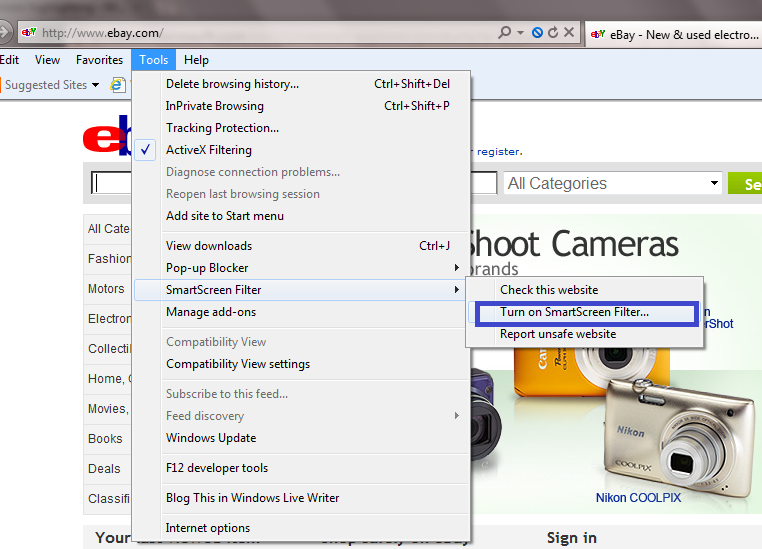
Internet Explorer Security Settings Configuration Guide
The foundation of safer browsing experience depends on how much secure your web browser is. When you install any web browser such as Internet Explorer, you get a default security setting, which may not be suitable for your web privacy and data integrity.This article aims to help you to learn a few useful security tips of Microsoft IE 9. With the new Internet explorer version 9 … [Read more...] about Internet Explorer Security Settings Configuration Guide