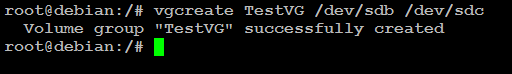
You may need to add new disk to your Linux LVM for various reasons such as for adding capacity for your existing applications or new applications. This post aims to show you how you can add a new disk to your existing LVM as well as to a new LVM. The difference between adding a new disk to a new LVM and to an existing LVM is that in the latter case you do not have to create a … [Read more...] about How to Extend Linux LVM by Adding a New Hard Disk
linux
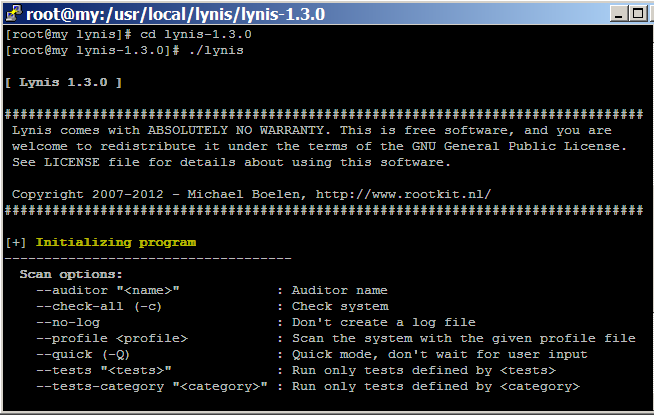
How to audit Linux CentOS Security with Lynis
Hardening Linux security may seem to be a daunting task for new Linux administrator and security auditor if they try to do it manually. Lynis automates the process of Linux security audit, which is widely used by system administrator, IT security auditor and security specialists. When you run Lynis to scan a system, it generates a report and suggestions that helps to patch up … [Read more...] about How to audit Linux CentOS Security with Lynis
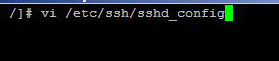
How to Disable Root Login Via SSH in Linux
Having the option of logging in to your server with SSH is essential for some web administrators, but logging in your server with root credentials via SSH is always unsafe. By the word root credentials, I mean that you should not remotely login with your server with root user name, rather use a less privileged user to login to your server and then use the "su" command to login … [Read more...] about How to Disable Root Login Via SSH in Linux
Linux Security Basics
The purpose of the Linux security checklist is to help the Linux users, entry-level, to become familiar with the most common security vulnerability of Linux operations systems. As you know security checking needs to be verified against well established practices, the following steps are necessary to following before starting your Linux security checking. Version number of … [Read more...] about Linux Security Basics