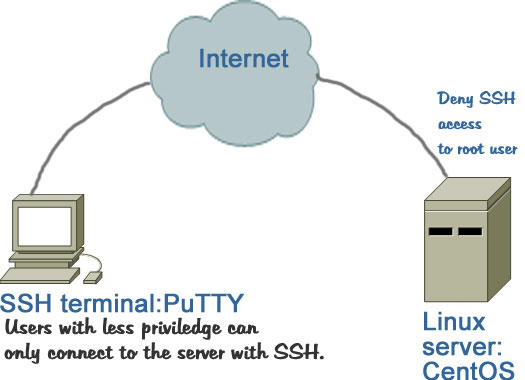
Having the option of logging in to your server with SSH is essential for some web administrators, but logging in your server with root credentials via SSH is always unsafe. By the word root credentials, I mean that you should not remotely login with your server with root user name, rather use a less privileged user to login to your server and then use the “su” command to login as a root user.
So, the purpose of this post is to show you:
- How to disable SSH with root username?
- How to enable a normal user to login with SSH?
- How to use root username after login with less privilege user name?
Step 1
If you have already installed your Linux server, you need to make sure that you have created a user with password. For example, you want to create a username chris, use the following commands:
#useradd chris
#passwd chris
Next type the password for the username chris.
When you type the above command a directory for the username will be created. If you want to delete a user name, type the following command:
#userdel –r username
Step 2
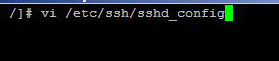
Now that you have a user other than the root user. So, you can safely deny the root user to access your server via SSH. To disable ssh root login you have to go to the following file:
Vi /etc/ssh/sshd_config
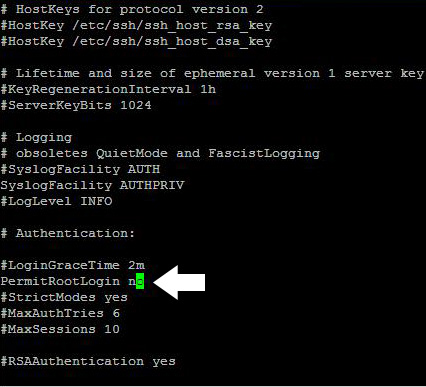
And then remove # from the line permitrootlogin. In vi editor, you need to press ”i” to enter in the insert mode. Then, use the backspace to remove the hash from the permitrootlogin and write no, instead of yes. After editing, your line should look like the following:
Permitrootlogin no
To save the changes press “w”. use the ESC key to go back to the command mode in the vi editor. Finally, use type :quit to go back to our shell prompt.
Step 3
Now, restart sshd with the following command:
service sshd restart
The steps described above prevent Linux root login via SSH. Preventing SSH root login improves Linux security and considered top priority when IT security auditor assess Linux for security vulnerabilities.