Hardening Linux security may seem to be a daunting task for new Linux administrator and security auditor if they try to do it manually. Lynis automates the process of Linux security audit, which is widely used by system administrator, IT security auditor and security specialists. When you run Lynis to scan a system, it generates a report and suggestions that helps to patch up the security loopholes. The following are the procedures that you can perform straightway without anyone’s help.
Supported platforms: Red Hat Enterprise Linux (RHEL), CentOS, Debian, FreeBSD, Ubuntu, Linux Mint and some other version of Linux. List of all supported platforms can be found at rootkit.nl/projects/lynis.html
In this instance, I have run all the mentions command in Cent OS 6.4
Create a directory for extracting Lynis files
At first create directory in /usr/local
To create a directory use the following command
# mkdir /usr/local/lynis
To download Lynis to your Linux server, you have to type the location of the lynis file, which is http://www.rootkit.nl/files/lynis-1.3.6.tar.gz
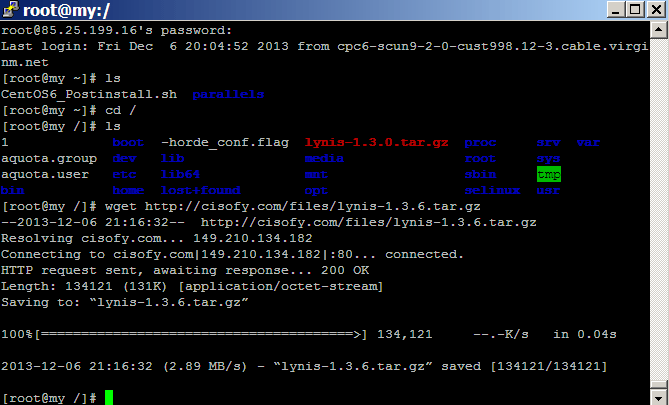
Remember to login as root user when you download it to your Linux server. To start download, type of following command from the lynis directory. It takes only a few second to complete the download.
# wget http://cisofy.com/files/lynis-1.3.6.tar.gz
For updated version you can check out at http://www.rootkit.nl/projects/lynis.html
Copy the .tar files to the new directory
Next, copy the downloaded file to the lynis directory that you created in step 1. The command for it:
cp lynis-1.3.6.tar.gz /usr/local/lynis
Use the the following command in the same directory to extract the files.
Lynis]# tar xzvf lynis-1.3.6.tar.gz
Next enter the extracted directory using the following command
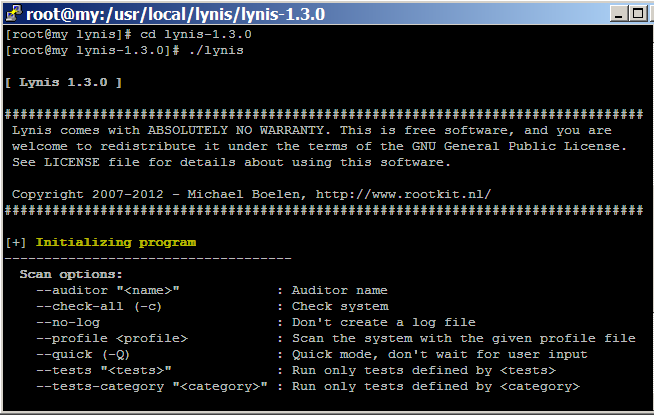
lynis]# cd lynis-1.3.6
Start audit and Scan
To see the complete set of lynis parameters type
lynis]# ./lynis
To start scanning, you can choose from two options. One option run all the security checks at a time and another option needs your intervention.
To see all the available scan options, execute the following command:
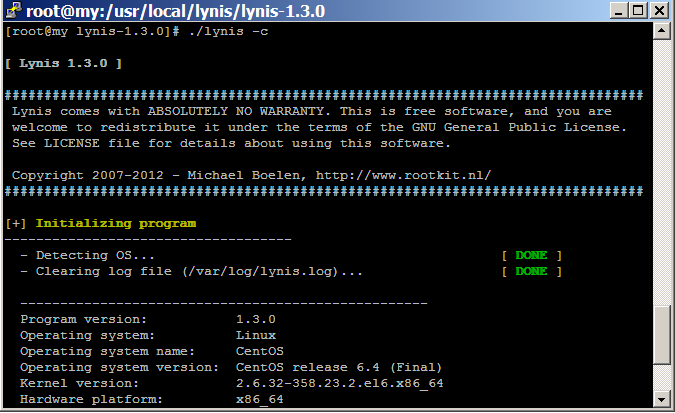
# ./lynis -c
To run all the check at a time, use the following command.
[root@my lynis-1.3.6]#./lynis -c –Q
Or
[root@my lynis-1.3.6]# ./lynis –check-all
If you want to intervene between each audit step type the following command
Lynis]#./lynis -c
Lynis stored the log of audit report in /var/log/lynis.log file. to enter the log file
Go to /var/log and then type
vi lynis.log
Here I am using Vi editor to see the text, you can choose any editor you like.
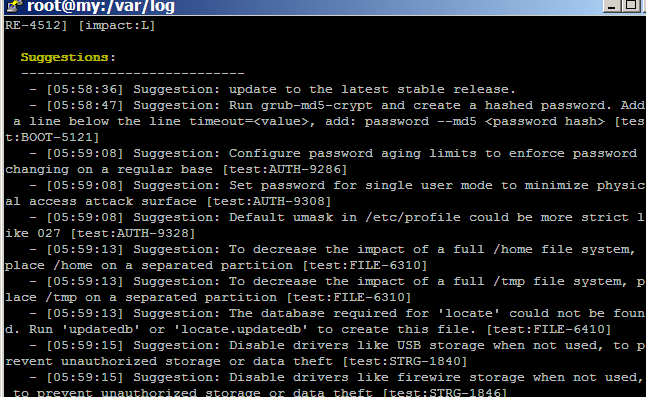
At the end of the log file, you will get a list of suggestions to rectify the security holes of your server.
Lynis update regularly, to check if you have updated version, type the following command
# ./lynis –check-update
When you update to new version remember to delete both the tar and extracted files in the lynis directory that you created at the first step of the post.