What is Identity Theft? You must have heard about ‘impersonation’ or identity fraud-the way one Internet user take on another user’s identity and gain illegal access of another user’s emails or data files. Annually almost 750,000 people are being affected by impersonation-the number one consumer complaint filed with FTC(Federal Trade Commission). The technical name of … [Read more...] about Identity Theft Protection Explained
Internet Security and Safety
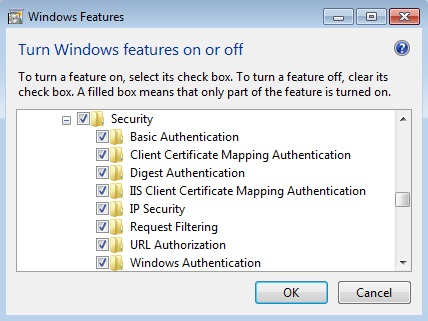
IIS Security Settings
The version of IIS is all about its modules and functions. If you are just learning IIS then before reading this article, it is better to take a closer look at the IIS manger on your server and then go through the following instructions. To secure your IIS server you need to put some extra care to the following settings of IIS server IIS authentication IPv4 and domain … [Read more...] about IIS Security Settings
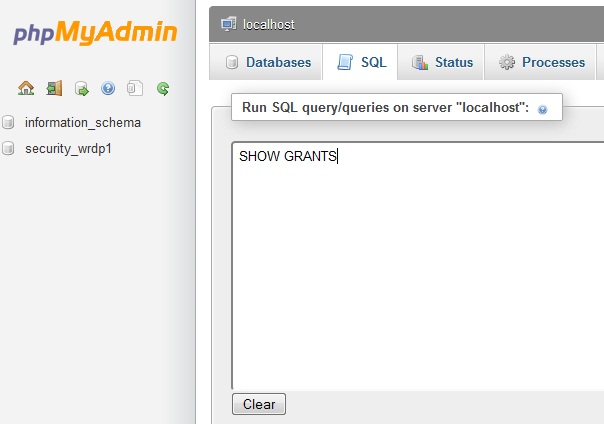
MySQL Security Settings Checklist and Issues
Securing MySQL requires not only hardening the security configuration of your database itself but also the web server along with the operating system. As you know that most of the web hosting provider love Linux and Apache as part of their web-hosting solution, you need to make sure that your host is taking proper security measures to ensure tighter control of Apache and OS. … [Read more...] about MySQL Security Settings Checklist and Issues
CMS Planning : WordPress Vs Drupal Vs Joomla
Building a website or blog with CMS such as Wordpress, Joomla or Drupal seems quite easy and requires only a few clicks on your host panel to bring your site online. What is the most important factor when you build a CMS based site is that you need a long term plan for the growth and expandability in terms of users, features, web space or even hosting. Let’s take a look at what … [Read more...] about CMS Planning : WordPress Vs Drupal Vs Joomla
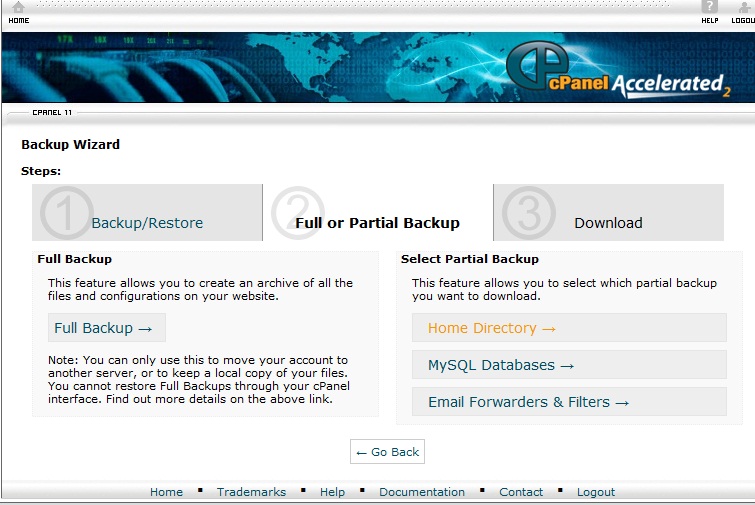
WordPress Backup & Restore:Database and Home Directory
There are thousands of wordpress experts who will suggest the beginners to take regular backup of their websites. If you are just learning how to make wordpress blog, then you may not pay attention to the importance of taking backup and restoration. Think about this you have a blog of 50 articles and getting 1000 organic traffic and one day morning when you logon to your … [Read more...] about WordPress Backup & Restore:Database and Home Directory
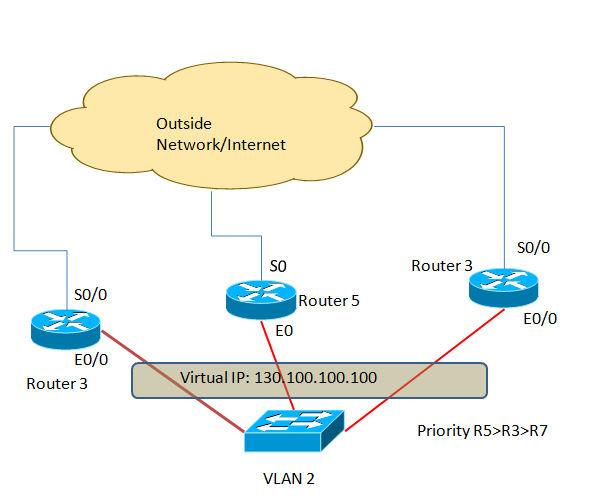
HSRP Configuration(Hot Standby Routing Protocol)
HSRP or hot standby routing protocol provides network redundancy solutions to routers.By configuring HSRP in a number of routers in a network you can offer your customers the opportunity to enjoy seamless network or Internet access opportunity. HSRP is mainly used in the perimeter network or in a network where high-available is a must or has zero tolerance to network downtime. … [Read more...] about HSRP Configuration(Hot Standby Routing Protocol)
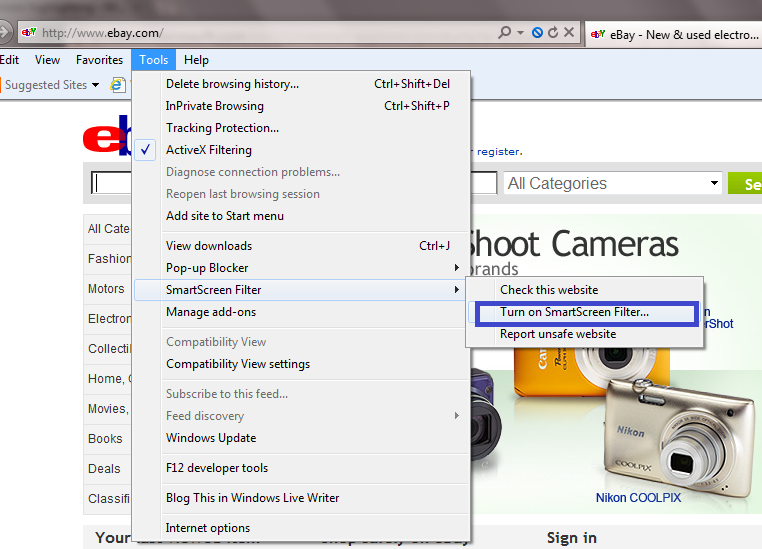
Internet Explorer Security Settings Configuration Guide
The foundation of safer browsing experience depends on how much secure your web browser is. When you install any web browser such as Internet Explorer, you get a default security setting, which may not be suitable for your web privacy and data integrity.This article aims to help you to learn a few useful security tips of Microsoft IE 9. With the new Internet explorer version 9 … [Read more...] about Internet Explorer Security Settings Configuration Guide
Facebook Security Issues| Checklists
Ever since Facebook has become an inevitable part of many of the Internet users, though not all, the cyber criminals are taking the advantage of Facebook users who does pay very little attention about the security of this giant social networking site. One of the most interesting thing is that many of the Face book users even has no knowledge about how much treats or what kind … [Read more...] about Facebook Security Issues| Checklists
Gmail Security Settings Checklist for Secure Login
Whether you are new Gmail User or not, one thing is true that you don’t like to lose your privacy or don’t want to your email security be compromised by any third party or by your business competitors. For making sure that your Gmail account is fully secure and no one is snooping your private emails, you need to follow several steps which are also recommended by Gmail … [Read more...] about Gmail Security Settings Checklist for Secure Login
Computer Security Essentials
The major threats a computer user may expect are – the damage of his stored data or software and stealing of confidential information. A computer can get infected with malicious programs like virus, Trojan, crimeware, spyware, malware or anything else, but the main challenge in front of you is to keep your all the data safe and also to keep your confidential information private … [Read more...] about Computer Security Essentials