One of the most easy to use tool for the beginners is that eskctl that help to quickly deploy Kubernetes cluster in AWS. We will share with you easy 3 steps creating a AWS managed EKS cluster with one EC2 worker node. To access the cluster we will install a dashboard using kube proxy that will allow you to access the dashboard from your local machine.
- install eskctl tool
- create the cluster
- setup the dashboard.
- Install eskctl tool
choco install -y eksctl
reference to install eskctl in Windows/Linux/Macos: https://docs.aws.amazon.com/eks/latest/userguide/eksctl.html
https://docs.aws.amazon.com/eks/latest/userguide/eksctl.html
- Create a EKS cluster
Create a cluster.yml file and add the following code. Make sure to replace the cluster name, region, VPC id, subnets and security group to match your requirements.
apiVersion: eksctl.io/v1alpha5
kind: ClusterConfig
metadata:
name: eks-cluster
region: eu-west-1
vpc:
id: "vpc-fec94a98"
securityGroup: "sg-52624428" # this is the ControlPlaneSecurityGroup
subnets:
private:
private1:
id: "subnet-0d323c180221aa9be"
private2:
id: "subnet-0ae45d49651f05b6d"
private3:
id: "subnet-0f56fc6f47d700b50"
public:
public1:
id: "subnet-7ea97f18"
public2:
id: "subnet-1371d55b"
public3:
id: "subnet-23352578"
nodeGroups:
- name: ng-1
instanceType: t3.micro
desiredCapacity: 1
- name: ng-2
instanceType: t3.micro
desiredCapacity: 1
- create dashboard
Make sure kubectl is installed in your local machine.
Run the below command to download and install the dashboard.
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.0.5/aio/deploy/recommended.yamlDownload the u
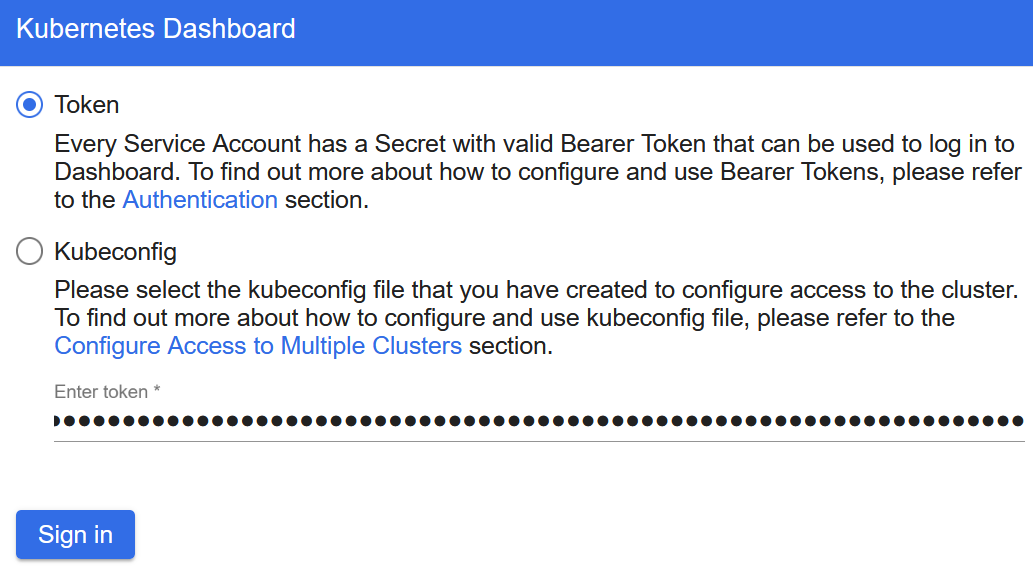
To connect to the Kubernetes dashboard, get the secret and copt it.
kubectl -n kube-system describe secret $(kubectl -n kube-system get secret | grep eks-admin | awk ‘{print $1}’)
Next, start the kube proxy
kubectl proxy
Paste the followng URL in the brower and the enter the token that you copied earlier
http://localhost:8001/api/v1/namespaces/kubernetes-dashboard/services/https:kubernetes-dashboard:/proxy/#/login
To completely remove the cluster aloing with the worker nodes, run eksctl delete command and make sure to replace
the name of the cluster “eks-cluster” by your cluster’s name.
eksctl delete cluster –name eks-cluster –region eu-west-1
References:
https://docs.aws.amazon.com/eks/latest/userguide/dashboard-tutorial.html
https://docs.aws.amazon.com/eks/latest/userguide/dashboard-tutorial.html [2] – https://www.eksworkshop.com/beginner/
