The demand for professional IT auditors is greater than ever due to the increasing digitalization of every aspect of business and industry. Starting a career as an IT auditor involves a combination of education, experience, and strategic planning. Here are ten tips to help you begin and succeed in this field: … [Read more...] about Top 10 Tips to Start a Career as an IT Auditor
audit
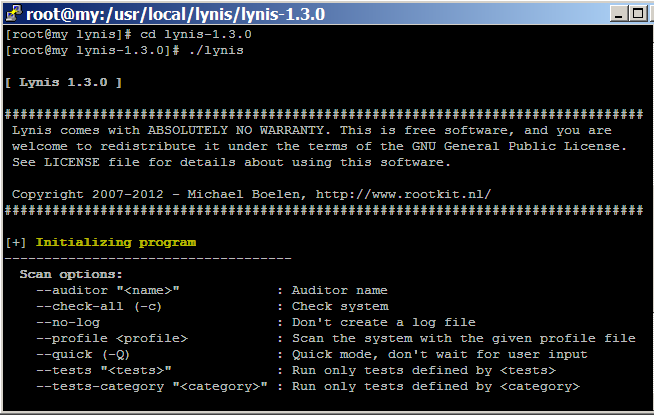
How to audit Linux CentOS Security with Lynis
Hardening Linux security may seem to be a daunting task for new Linux administrator and security auditor if they try to do it manually. Lynis automates the process of Linux security audit, which is widely used by system administrator, IT security auditor and security specialists. When you run Lynis to scan a system, it generates a report and suggestions that helps to patch up … [Read more...] about How to audit Linux CentOS Security with Lynis
Audit Charter Explained
What is an Audit charter? An audit charter is the base of an audit because every auditor starts his audit with an audit charter. In simple words, an audit charter defines the responsibilities, authority and accountability of an auditor along with the scope of the audit. Normally, a charter also specify the management’s responsibility and their delegation of authority to the IS … [Read more...] about Audit Charter Explained
Cisco Router Security Check for Auditor
Since router is the key to access an organization's network from the outside world, the maximum security priority should be given to routers that are connected to the Internet and to the important application servers. ISO-27001 has already defined standard router security checklist, which any organization can use to improve their router securities. This post aims to … [Read more...] about Cisco Router Security Check for Auditor